



























Control ‘who’ can access ‘what’. Audit, monitor, and record all activity. Automate password management best practices. Ensure compliance with standards, reduce security risks.
Sanmarco Informatica, a leading Italian digital services provider centralized credential management, strengthened compliance, and boosted managed services efficiency by 60% with Securden.
Watch Video
Securden is perfect for managing a large volume of secrets in an enterprise environment. The best thing about this software is ongoing follow-up for its continuous improvement. It adapts well to different situations and offers very interesting functionalities, such as accessing systems without having to copy and paste the password. The user interface is convenient, and it includes browser plugins to speed up access. It’s really easy to use.

One of the many things we love about Securden Password Vault For Enterprises is its amazing access control features (for example, we can hide folders for some users while giving permissions to others). Plus, the ability to launch web RDP and web SSH sessions has been helpful. Their customer support is extraordinary—we’ve always received immediate solutions to any problems we’ve faced.

Securden's team is very communicative and responsive. Can never rave enough about them. I can never rave enough about Securden. We came to them with a large obstacle that other password managers could not achieve, and they built it out within a month. Anytime we have an issue, they are immediately on it. They are very communicative, and responsive.




















































Offer privileged access management as a service for your diverse client base.
Leverage the power of industry-first, truly purpose-built design.
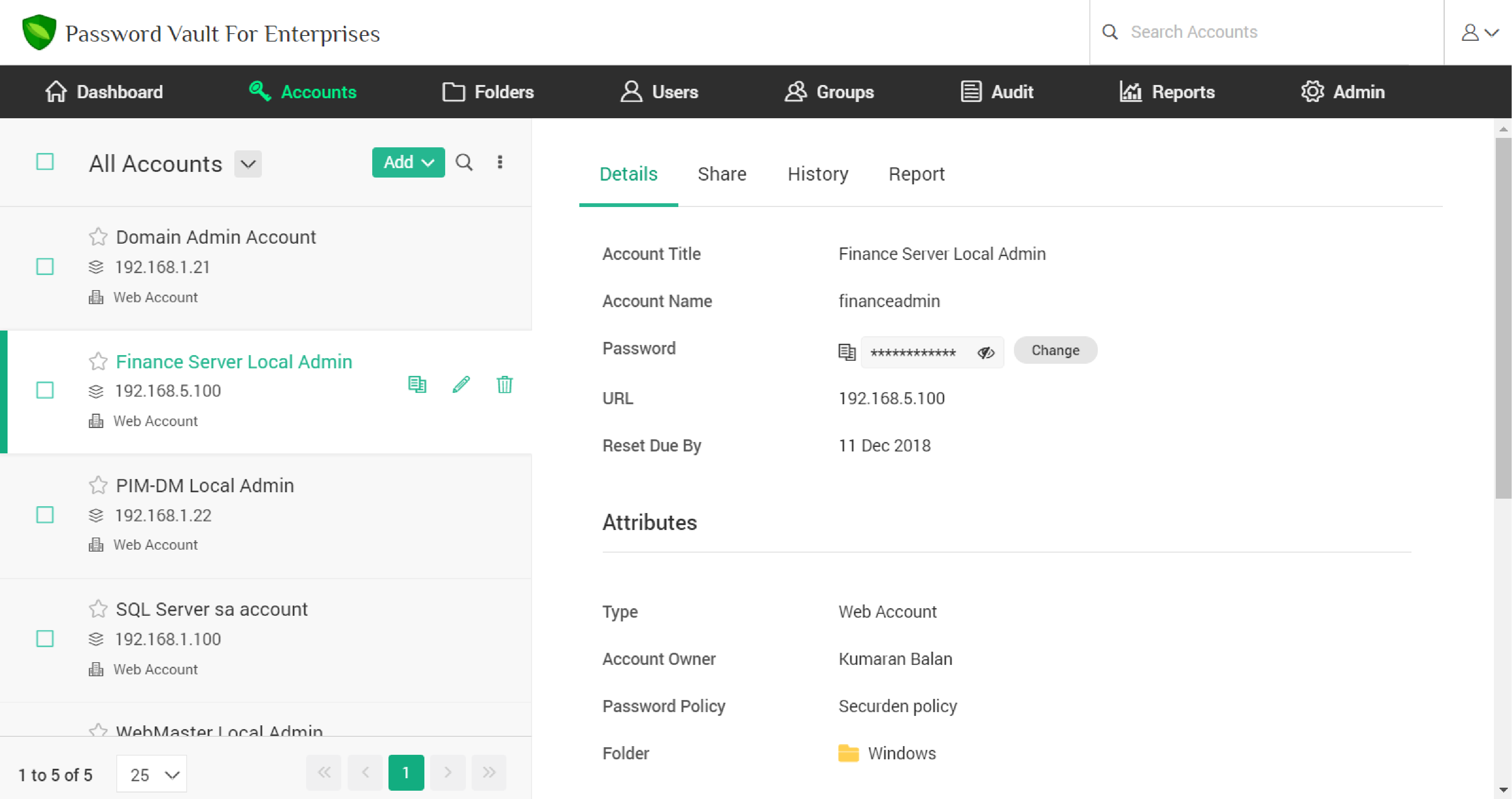
Securden Password Manager simplifies the way your organization manages sensitive enterprise passwords and allows you to collaborate more effectively.
Securden Password Manager locks down passwords, access keys, files, and other sensitive data used in your enterprise in a central vault and protects them. The reports and logs provide complete visibility on who has access to what data. It also throws light on password hygiene across the organization and helps administrators bolster internal controls.
When sensitive accounts are shared with many users in the team, it becomes difficult to trace actions to an individual. Through centralized access controls, Securden enterprise password manager tracks all access to shared accounts across the enterprise. As a result, activities can be directly traced to individuals. With password manager for teams, you can establish clear accountability and ensure that every access request is properly logged and monitored.
The decentralized way of enterprise password management leads to system lockouts, forgotten passwords, password fatigue, and results in frustration for employees. Users may circumvent by using simple passwords or reuse the same password everywhere. Securden Password Manager removes all these hurdles and seamlessly enforces password hygiene and improves productivity across the enterprise.

The whole idea of enterprise password management made refreshingly simple, secure, efficient, reliable, and affordable.
Securden Password Manager handles your passwords and other critical data with extreme security. Sensitive data are encrypted using AES-256, the strongest known, military-grade algorithm.
Each installation is guarded by a unique encryption key. In production instances, the encryption key will be forced to be kept outside the installation. The idea is not to allow the encryption key and encrypted data to stay together. The backup data of Securden database is also equally guarded. Without the encryption key, the backup data cannot be deciphered.
In addition, SSL/TLS has been enforced on all connections / communication, which ensures end-to-end, complete encryption.
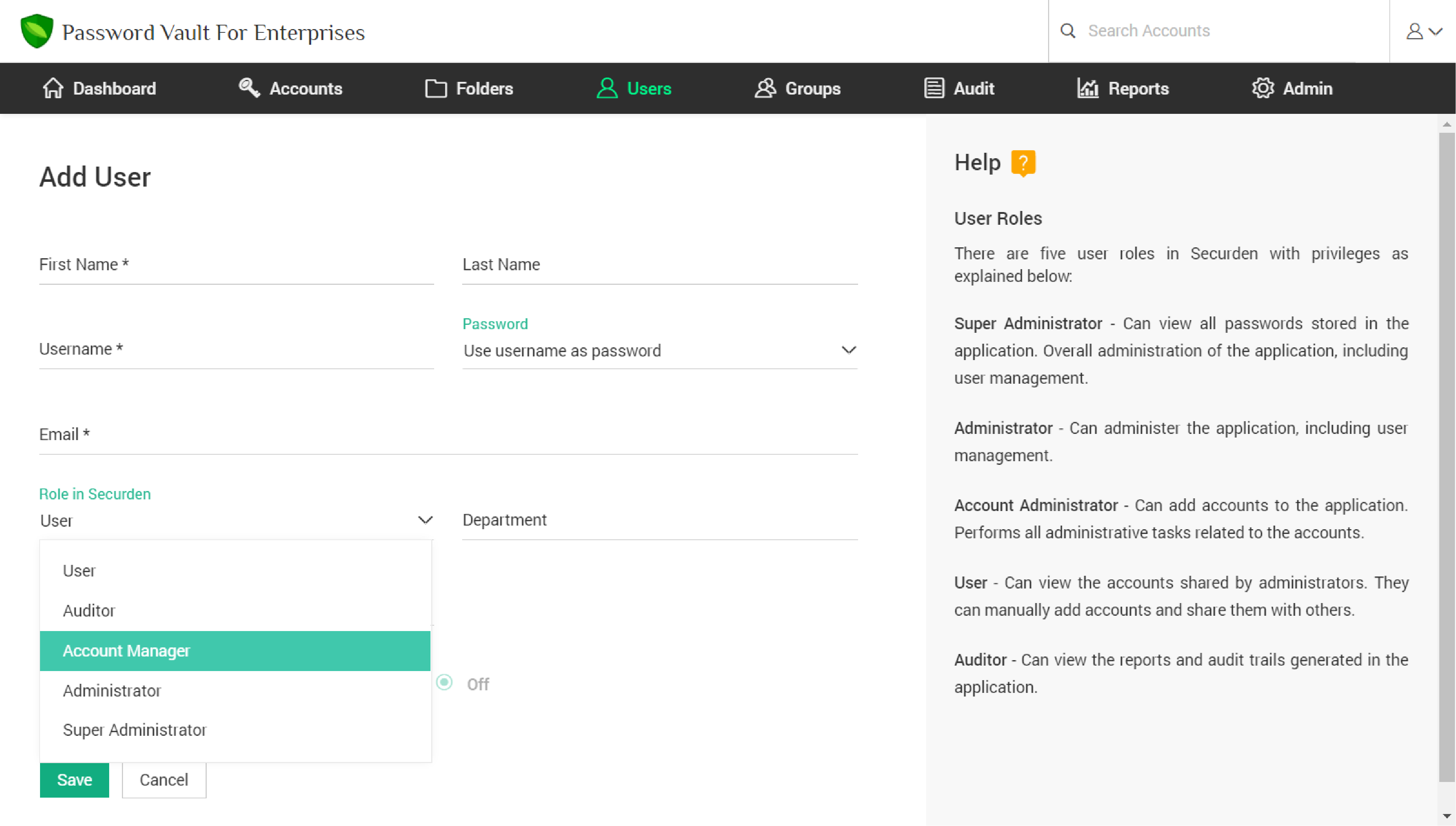
Every team member or group in your enterprise will have varying requirements. Securden Password Manager provides role-based access controls to grant access to passwords strictly based on their job requirements.
The role-based access to credentials is further strengthened with fine-grained controls. Access permission could vary from full access to just view/edit passwords and in extreme cases, access with hidden passwords.
At the application level, the ability to add accounts, create and manage users, enforce password policy, export data, and change settings can all be controlled through roles.
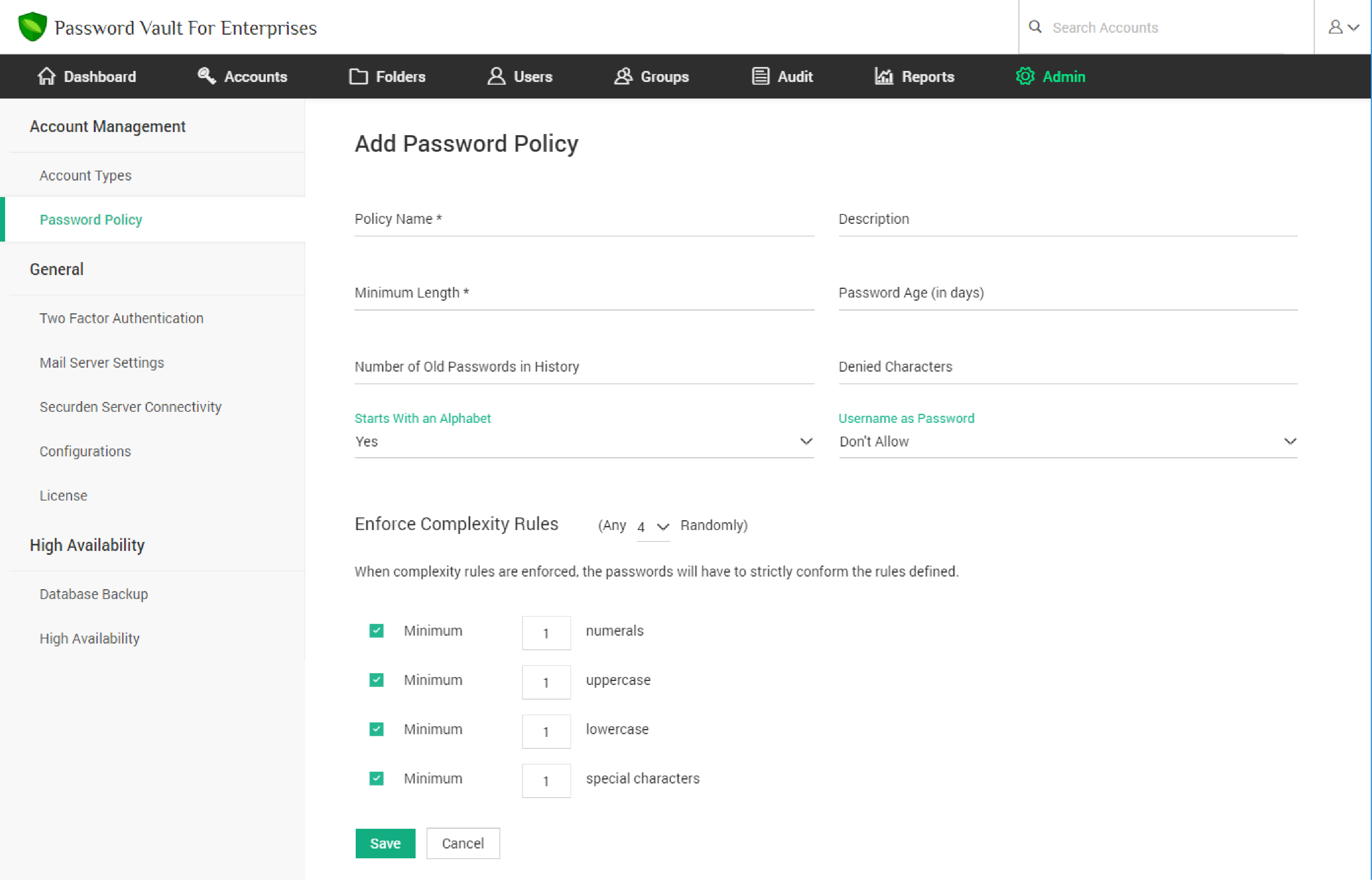
Data breaches often occur due to weak passwords. Assigning strong, unique, random passwords across all IT assets and applications across the enterprise will help in mitigating this crucial security vulnerability.
Securden Enterprise Password Manager offers provision to create password policies that define complexity requirements. Securden also archives old passwords. Your password policy could even prevent reuse of old passwords. Password age could also be defined, beyond which the expiration alerts could be generated.
The password generator that comes with Securden generates strong passwords based on the policy defined. The random passwords would be virtually impossible to guess. You can assign the complex passwords to the IT assets and securely lock them down in the vault.
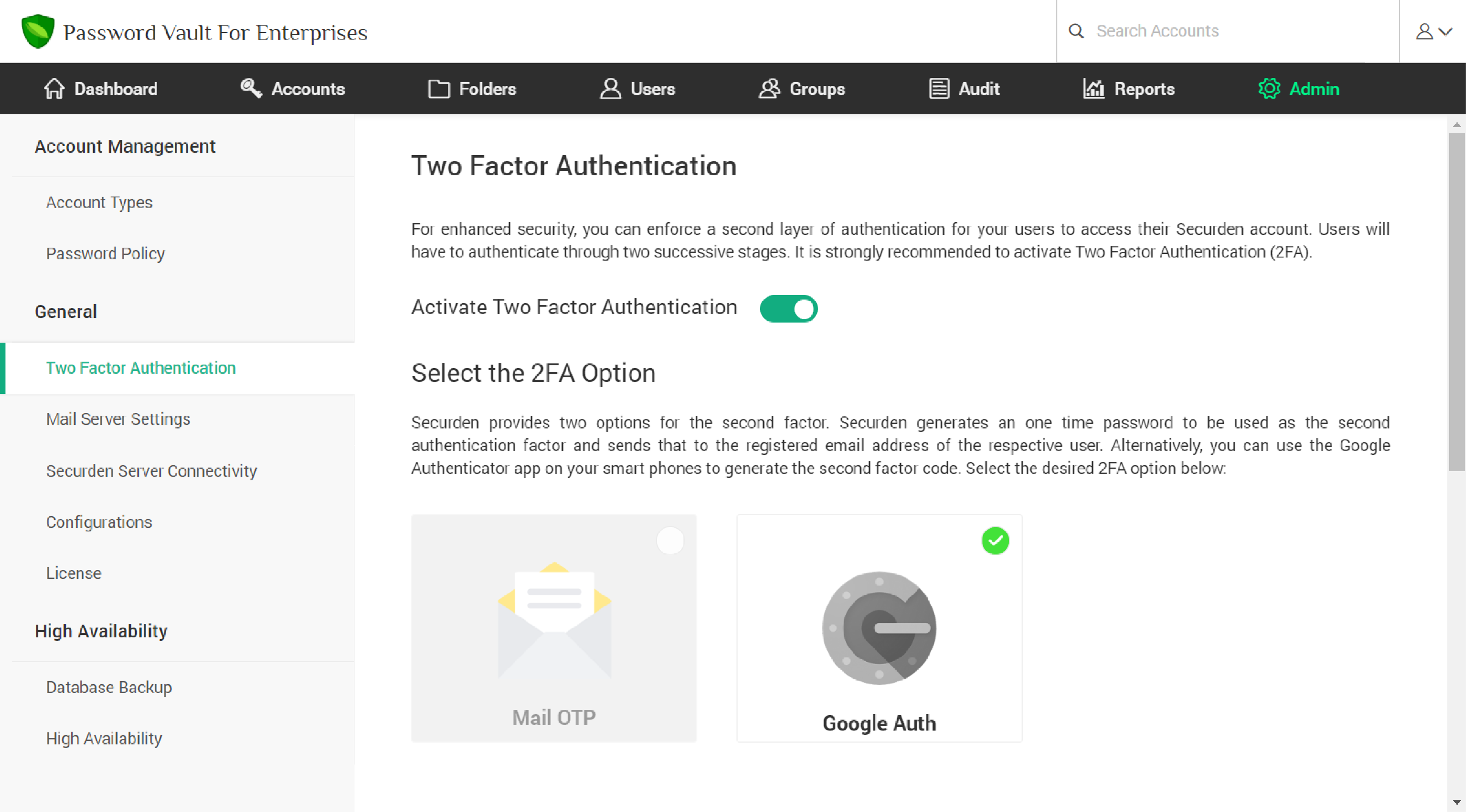
Software applications that require two or more successive authentication factors to grant rightful access are difficult to break.
By enforcing users to authenticate through two successive stages to access their Securden Password Manager account, you can successfully prevent any possible accidental or intentional unauthorized access to Securden. Securden's native authentication or Active Directory authentication serves as the primary authentication mechanism.
Additionally, users can be forced to authenticate through Google Authenticator or verification code sent to their email address as the second authentication factor. You can selectively enforce any option as the second authentication factor for different users as required.
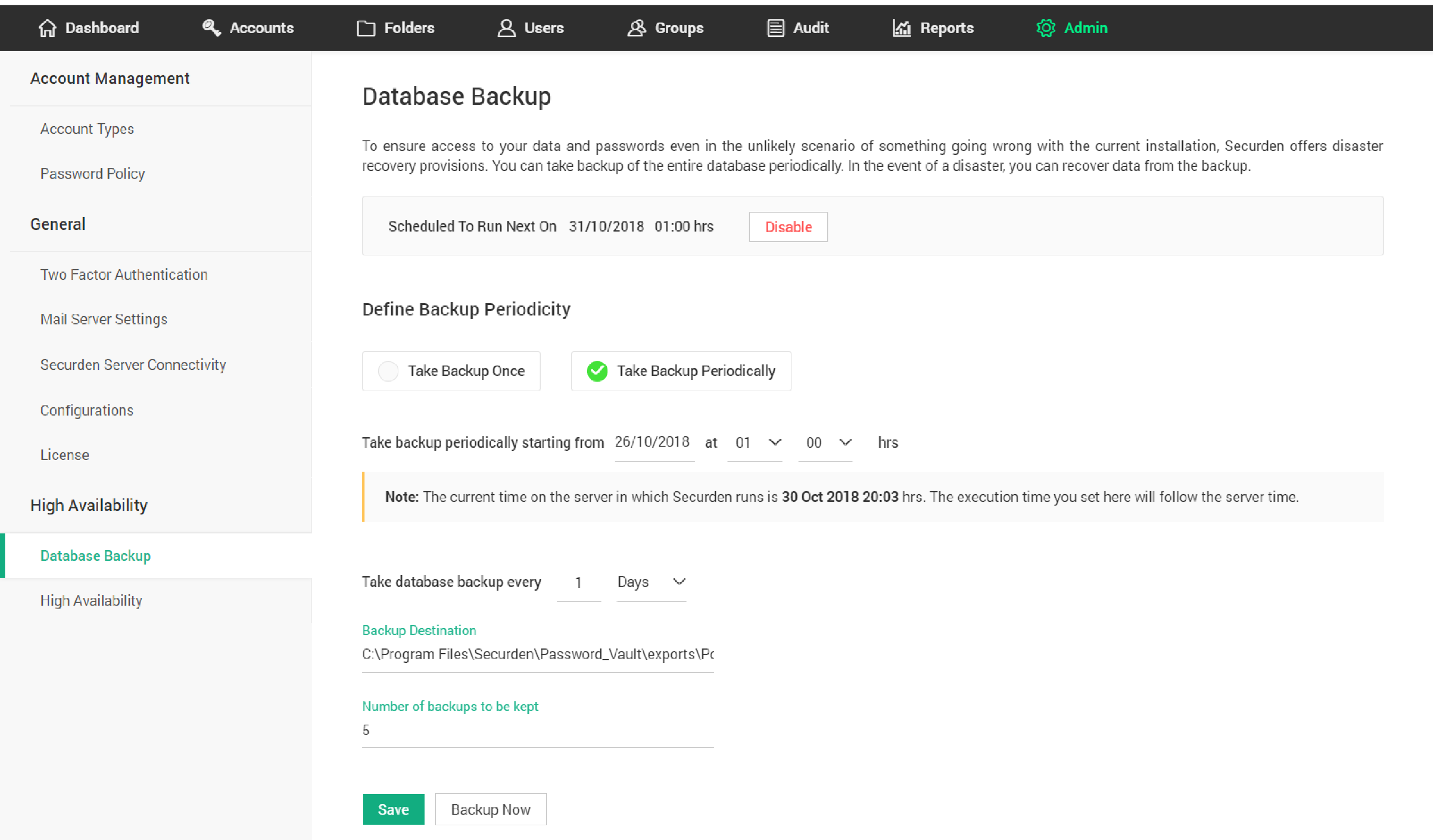
Unexpected downtime or system crash could take a heavy toll on the business continuity and data security of any enterprise.
Securden Password Manager comes with a robust redundancy architecture allowing you to have primary and secondary application servers. If the primary server goes down, users can seamlessly connect to the secondary server and get uninterrupted access to credentials.
Securden Password Manager also comes with provision for periodic backup of the database and a smart recovery manager that takes care of a quick recovery in the unlikely event of a database crash.
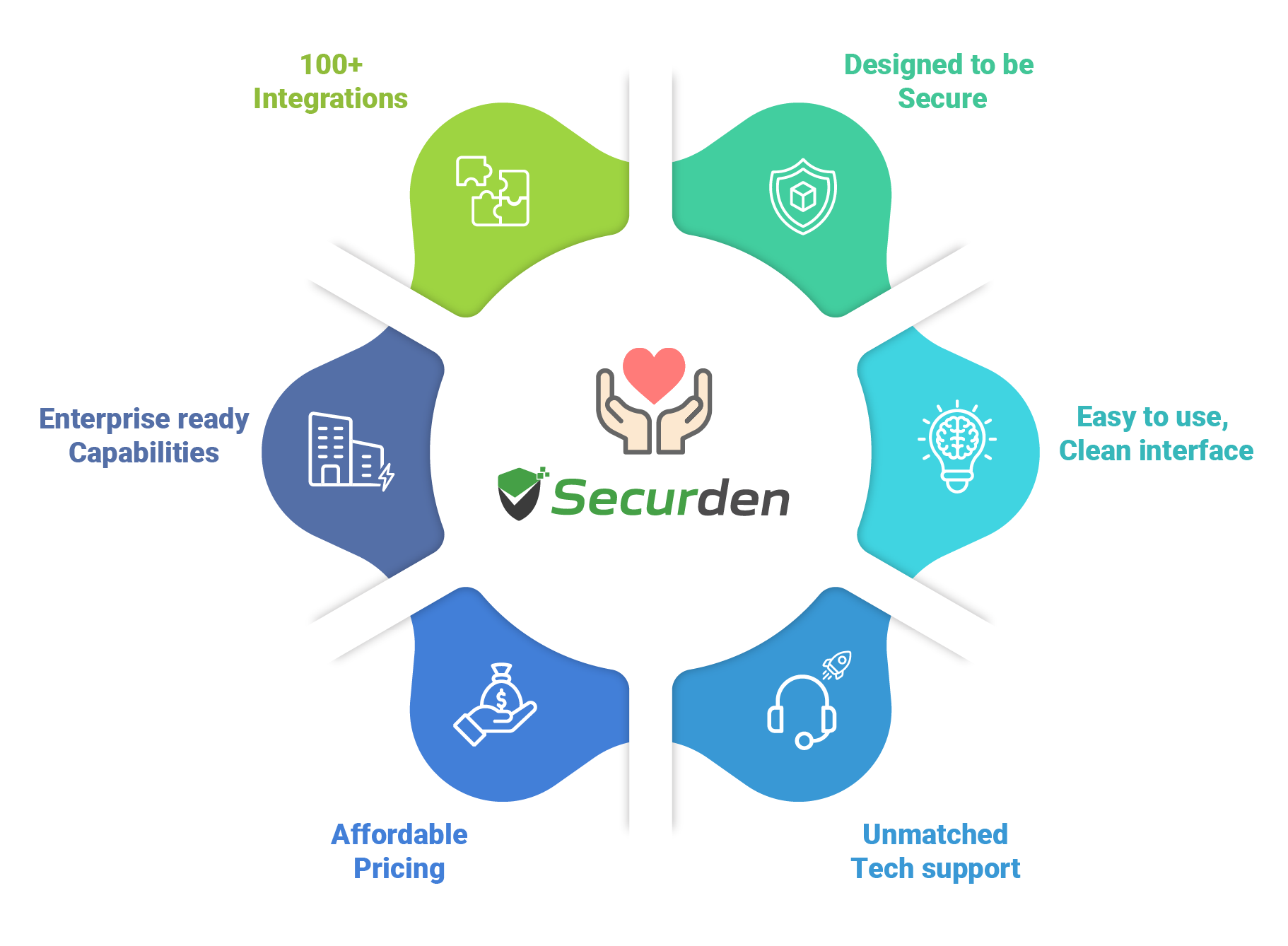
At Securden, we're fanatical about one thing:
Creating amazing products that combine security, simplicity, and affordability.
Organizations of all types and sizes - from small businesses to very large enterprises - are relying on Securden for information security.
Here's what sets us apart from the rest.
Securden readily integrates with your existing tech stack and provides a seamless deployment experience. Explore the supported integrations with SSO providers, MFA solutions, directories, SIEM solutions, and cloud storage services.


































































































IT security specialists from a UK-based firm performed various penetration tests and concluded that Securden is well-built with a top-notch security model. Learn More.

-- Experts from Agile Infosec, London.
Take the best first step in information security with Securden enterprise password management software.


A password manager provides a centralized, encrypted vault to protect logins, keys, DevOps secrets, and other sensitive information across small to mid-sized teams and enterprises. It simplifies credential management by enabling strong password creation, autofill for seamless access, and granular, just-in-time access controls. Advanced features such as audit trails, sharing MFA tokens and risk intelligence offered by Securden Password Vault for Enterprises, further enhance compliance, visibility, and defence against cyber threats.


Absolutely. A password manager is essential for enterprises seeking to securely centralize logins, keys, and other sensitive credentials. It eliminates risky practices such as password reuse or storing credentials in spreadsheets, enforces strong security policies, and enables secure team sharing with granular, role-based access controls. Just-in-time access for third-party stakeholders and vendors, along with comprehensive audit trails, helps ensure compliance.
In addition to enhancing security, a password manager streamlines onboarding, automates credential rotation, manages DevOps secrets, and boosts efficiency across teams. Securden Password Vault for Enterprises offers all the above-mentioned features in both SaaS and on-premises deployment models, catering to small to mid-sized teams and enterprises.


A password manager operates by encrypting all enterprise credentials and storing them in a secure, centralized vault. After a single/ multi-factor authentication, users can access only the credentials they are authorized to use. It enforces robust password policies, generates strong and unique logins, and enables secure autofill without exposing plain-text passwords.
Advanced features such as granular, role-based access controls, just-in-time credential sharing, and comprehensive audit trails help ensure compliance and prevent misuse. Automated processes rotate credentials, manage DevOps secrets, and streamline access for distributed teams. Securden Password Vault for Enterprises delivers these capabilities in both SaaS and On-prem models, tailored for small to mid-size teams and enterprises.


A self-hosted password manager is a solution deployed within your organization’s own infrastructure which could be either on-premises or in your private cloud, so you retain complete control over your sensitive credentials and data. Unlike cloud-hosted options that store information on third-party servers, a self-hosted password manager lets your IT team manage storage, access policies, backups, and updates internally.
Securden Password Vault for Enterprises offers both a fully self-hosted deployment model and a SaaS model, to suit enterprises that need flexibility in balancing complete data control with cloud-based convenience.


The choice depends on your organization’s security, compliance, and operational needs.
A Cloud Password Manager (SaaS model) is ideal if you want quick deployment, automatic updates, and minimal IT maintenance. It allows teams to access credentials securely from anywhere and scales easily as your business grows.
An On-Premises or Self-Hosted Password Manager is best suited for organizations that require complete control over data, strict regulatory compliance, or operate in isolated network environments. It gives IT teams full authority over hosting, data storage, and access policies.
Securden Password Vault for Enterprises offers both deployment options (SaaS and on-Prem), so you can choose the model that aligns best with your infrastructure, compliance goals, and internal security posture.


Securden Enterprise Password Manager is a comprehensive solution for enterprises to store, manage, and automate all password management operations. It also enables secure password sharing and controls user access permissions to critical resources.


Securden Enterprise Password Manager should be hosted on a Windows server, but the vault can be accessed from devices running any operating system including Windows, Linux, Mac and so on. You can deploy the product on-premises within your IT environment, host it on private cloud instances, or have a complete SaaS deployment. For more details, visit https://www.securden.com/password-manager/password-management-deployment-options.html


Securden Enterprise Password Manager software employs AES-256 encryption, the strongest military-grade algorithm, to encrypt all sensitive and critical data. Each application installation is protected by a unique encryption key. The encryption key is kept separate from the data, ensuring that backed-up data cannot be decrypted without it. Additionally, SSL/TLS is enforced on all connections and communications, ensuring complete end-to-end encryption of data in transit.


Yes, Securden Enterprise Password Manager mobile application is now available for both Android and iOS mobile operating systems. It lets users add accounts, change account passwords, manage shared accounts, configure multi-factor authentication, and overall manage passwords on the go.


Securden Enterprise Password Manager functions as a comprehensive enterprise-grade password lifecycle management software, offering much more than just storing passwords. Some of the features that distinguish it from other enterprise password management solutions include:


Securden Enterprise Password Manager stores all passwords in a centralized, encrypted vault. It enforces granular access permissions for all sensitive data, automates enterprise password management operations like password rotation, and helps track shared password usage across the enterprise.


Securden Enterprise Password Manager comes in four different editions - Starter, Teams, Enterprise, and Enterprise PAM. To know the feature specifications of each edition, visit https://www.securden.com/password-manager/pricing.html


The pricing and licensing of Securden's Enterprise Password Vault software depend on both the number of users utilizing the application and the edition chosen by your organization. Price quote information can be received by filling out a simple form on the website - https://www.securden.com/password-manager/pricing.html


Securden Enterprise Password Manager has an inbuilt password generator that generates random, complex passwords based on the defined complexity rules and set password policy.


Once accounts are onboarded and passwords are set, admins can enforce specific password policies for individual or groups of accounts. By default, a Securden password policy applies to all accounts. Additionally, admins can create customized password policies to meet their business compliance standards. To set a password policy, navigate to Admin >> Password Policy. Here, you can define password complexity rules such as maximum characters, maximum length, password age, denied words, and more.


With Securden Enterprise Password Manager, you can store, organize, manage, and rotate passwords. You can also use the safe private vault to store all your sensitive keys, documents, and identities.


Securden Enterprise Password Manager is the safest way to manage all your enterprise passwords. It comes with the highest security standards and zero-knowledge encryption. No one has access to your data except you.


Yes, Securden Enterprise Password Manager is better for password generation than using your own passwords. You can set password complexity rules within the platform. It generates unique, strong passwords and automatically auto fills passwords in websites. You can finally put a halt to weak passwords or reusing passwords across applications.


With Securden Enterprise Password Manager, all you need to remember is your encryption key. The encryption key must be stored outside in a secure place. It lets you unlock the encrypted password database.


Securden Enterprise Password Manager lets you organize and store all your passwords, keys, certificates, and other sensitive information. The encrypted password vault works on zero-knowledge principle, which means data is visible only to you. You must use your master password to unencrypt your vault.
In-built password generatorSecurden Enterprise Password Manager has a built-in password generator that keeps you away from password vulnerabilities. No more reuse of weak passwords – generate unique, complex passwords for all your accounts and implement security best practices.
