What is Privileged Access Management?
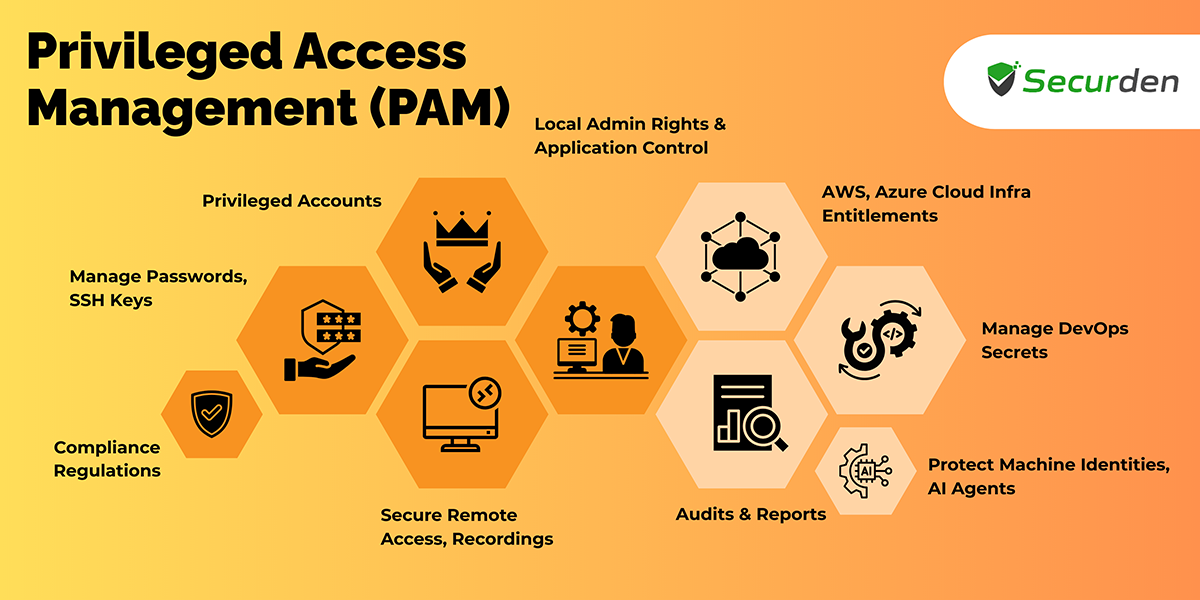
Privileged Access Management (PAM) can be defined as an IT security strategy that ensures the appropriate control of access to critical data and resources. It primarily involves securing privileged accounts, controlling privileged access granted to users, and governing all privileged activity carried out in the organization.
PAM safeguards privileged identities and gives them just enough access to do their day-to-day activities without a hassle. This helps organizations minimize their overall attack surface and mitigate security risks due to internal and external threats.
For example, the IT team of a healthcare provider has ongoing administrative access to medical records systems. It will be risky if any attackers could get into the system compromise them. If any of those accounts were hacked, attackers might get vital patient data right away - causing violations of several compliance regulations like HIPAA, GDPR.
What are privileged accounts?
Any login credential which grants privileges or administrative rights to systems and applications is known as a privileged account. These accounts can be associated with human users and non-human entities such as application and machine identities.
Privileged accounts can be of different forms/types. In an enterprise IT environment, these accounts exist in the form of administrator accounts, superuser accounts, root accounts, local administrator accounts, domain administrator accounts, secure socket shell keys (SSH keys), service and application accounts. These high privilege accounts are also called ‘secrets’ from a DevOps context.
It's crucial to know the different types of privileged accounts because they aren't all the same in nature.
What are the different types of privileged accounts?
There are seven types of privileged accounts each with different levels of access. They are
Domain Admin Account - Domain admin accounts have the highest level of access among the types of privileged accounts. These accounts have access to all the servers, applications, and accounts, and workstations. These possess privileges to modify the access rights of every admin account of systems within the domain and need to be restricted as much as possible.
Privileged Account - Any standard user account that has been granted elevated privileges is called a privileged account. They are essential for handling critical data and systems, but if utilized improperly, they pose serious security risks. Properly maintaining these accounts is essential to prevent unauthorized access and safeguard critical resources.
Local Admin Account - IT workers commonly use local administrative accounts, which provide administrative-level access to specific computers, to maintain endpoints, servers, network devices, databases, and other systems. These accounts are popular targets for cybercriminals looking to establish first access to a company's network and then move laterally within it as local admin accounts frequently use the same password across multiple devices.
Service Account - Applications and services use service accounts to make sure operating systems work properly and softwares run effectively. Depending on the needs of the application, these accounts may have domain admin privileges in certain cases. Even though service accounts aren't usually permitted to access systems, they frequently have passwords that are never changed or expire. Therefore, hackers commonly use these accounts as the target of attacks.
Emergency Account - An emergency account is considered a break glass account where the user can view all the accounts and credentials but can’t access it. Emergency accounts are activated to recover or restore the accounts in case of disasters.
Application Account - As the name suggests, application service accounts are a particular type of account used in IT environments to execute automated processes, applications, or services. These privileged accounts usually have significant access to data about the company that has been stored in databases and applications. These accounts' passwords frequently get stored in plain text files that aren't encrypted, leaving them vulnerable to attack by hackers looking for ways into a company's network.
Domain Service Account - These accounts integrate with several apps and systems, allowing them to interact and obtain required resources, usually for running reports, getting database access, or making API calls. Since updating a domain service account's password necessitates the account's logout, this may cause the application to break if the password is not correctly synchronized.
Now that we know the different types of privileged accounts, lets see how Privileged Access Management works to secure them.
How does Privileged Access Management (PAM) work?
PAM works by holistically securing all privileged access vectors i.e., people, processes, and devices for reducing the risk of a data breach and misuse of privileges by providing control and complete visibility over privileged access.
The first step in privileged access management system is to onboard the users who require access to the encrypted vault protecting the privileged accounts.
Next step is to bring all privileged accounts present in databases, network devices like servers, switches, routers, and other endpoints under the same umbrella for centralized management.
The privileged access management system enforces strong authentication and authorization mechanisms to ensure only the right users gain access to the privileged accounts present in the centralized vault.
PAM tools help enforce security best practices like automatically assigning strong unique passwords and deploying advanced security measures such as multi-factor authentication for preventing unauthorized access to the repository.
You can define and enforce access policies that help manage ‘who’ gets access to ‘what’ and ‘when’. These policies could help automate access workflows. Provisioning and revoking privileges can be automated to a great degree with the help of these policies.
For added security and control over critical assets, PAM provides real-time monitoring of live and recorded remote sessions. Organizations can monitor privileged sessions and respond to malicious activities if detected.
PAM tools help track and monitor privileged access by maintaining a complete trail of all activities involving privileged accounts. These audit trails provide complete visibility over privileged access and provide insights on ‘who’ did ‘what’ and ‘when’ using ‘which’ privileged accounts.
Knowing PAM best practices is more than just adhering to security regulations; it's also about making sure your privileged access approach is robust and effective.
What best practices should CISOs and IT administrators adopt for effective Privileged Access Management (PAM)?
Consolidate Privileged Accounts - Discover the privileged accounts existing in your network and consolidate them into an encrypted vault for centralized management. A siloed approach to privileged account management reduces visibility and is detrimental to demonstrating compliance with regulations. Centralized credential management helps manage access to PAM credentials and enforce security best practices efficiently.
Enforce Role Based Access Controls - As a key security practice, you should only grant just enough access for users to fulfill their duties. In most cases, end users don’t need access to view or modify privileged credentials. If an end user needs access to an IT asset, you need to grant access to the asset without revealing the credentials. This is done using granular role-based access controls. You need to associate privileges with user roles and assign these roles to the respective users. You can granularly select and assign privileges to user roles.
Enforce Password Security Best Practices - Password security best practices include a variety of measures ranging from basic steps such as assigning long, strong, complex passwords to more modern steps like enforcing MFA. Modern computing capabilities make cracking passwords using brute force techniques very easy. A long, complex password will ensure that your privileged accounts are secure against such attacks. Enforcing MFA on sensitive accounts helps protect against credential-based attacks. Attacks like credential spraying and stuffing, enforcing MFA will help prevent unauthorized access to IT assets.
Use Jump Hosts and TLS Encryption - End user machines are often the weakest link in any network. These machines are used to access resources on the internet, access emails, download files, etc. These machines carry lot of vulnerabilities in them. If end user machines are allowed to connect to sensitive IT assets directly, the privileged identities get exposed to all kinds of threats. To protect privileged identities, restrict users from establishing a direct connection with them.
Route all your connections through a jump host to ensure no direct connections are established between end user machines and sensitive IT assets. You can achieve this by launching connections to assets from a PAM solution. Launch connections to IT assets through VPN less RDP, SSH, and SQL connections and ensure your internal IT assets are secure. As an additional security measure, you can enforce TLS encryption for all connections launched to internal assets.
Enforce Just in Time Access - One of the core principles of privileged access management is to eliminate all standing access to sensitive IT assets. When a user account with standing access to sensitive assets is compromised, the intruder will implicitly gain access to the asset. To prevent this, access to sensitive assets should always be ephemeral. Users should be able to access the asset only when absolutely required. The access should start and end within the specified time. This way of granting temporary privileged access is called just-in-time access.
Privileged access management solutions can help automate JIT-based access provisioning and offer methods to instantly revoke access if required. Once the access is revoked, it is advisable to reset the password of the asset.
Monitor, Track Sessions - Sensitive accounts are often used by internal users and external vendors and contractors. What the users do within a privileged session should be closely monitored and completely documented. All privileged activities should be recorded as audit trails to maintain a complete record. These records help maintain compliance with regulations. When remote connections are launched to sensitive assets, the entire session should be recorded and stored for analysis. Administrators should be able to shadow live sessions without the user’s knowledge. If any malicious activity is suspected, the administrator should terminate the session immediately.
Remove Local Administrators - Eliminating local administrator rights on endpoints will help mitigate almost 90% of all vulnerabilities that exist in Windows operating system. You can restrict employees from clicking on malicious links and downloading malware onto endpoints in your network by removing their local administrator privileges. Most employees can perform their job responsibilities working with standard user accounts.
Enforce Principle of Least Privilege - To limit the threat surface of your organization, principles of zero-trust and zero-standing-privileges should be enforced. Zero-trust encourages organizations to adopt the policy of “Never trust, always verify” instead of the more traditional “Trust but verify”. One of the key action items in adopting Zero-trust is to enforce the principle of least privileges.
The principle of least privilege involves granting just enough access for the users to perform their duties. Granting just enough access at the right time eliminates productivity hurdles associated with eliminating local administrator privileges and making employees work with standard accounts.
Limit the Number of Administrators - Administrator accounts carry a lot of privileges with them and are often hot targets for attackers. Administrators make accessing sensitive information easy and are often involved in data breaches. To reduce the attack surface of the organization and protect sensitive information, the number of administrator accounts should be kept to a minimum.
Limit Privileges for Administrators - One of the most important privileged access management best practices is to not put all your eggs in the same basket. To perform administrative tasks efficiently and securely, privileges should be split between different administrative users. Separation of privileges will help enforce separation of duties.
Such a structure will also help promote maker checker controls and ultimately improve the overall security posture of the organization. To strike a balance between limiting the number of administrators and separating duties, you should take into consideration the size and complexity of your organization, the number of administrative tasks at hand and the privileges involved.
Isolate Privileged Resources in a Secure Network - Letting end user machines and privileged assets operate from the same network is not advisable. Human and non-human intruders can easily travel between devices in the network. To completely eliminate lateral movement of threat actors, privileged IT assets must be separated from the network in which end user machines operate. This is also addressed as network segmentation.
Network segmentation also helps curb malware and ransomware propagation from end user machines to privileged assets.
Why is PAM important for your IT teams?
Privileged Access Management is vital to protect privileged accounts and administer control over administrative access in your organization. It not only improves the overall security posture and also enhances operational efficiency across the enterprise. PAM is important for an organization:
To sense and prevent cyberattacks - PAM audits and logs all privileged activity, any changed password, launched application, or RDP connection taken can be used to raise an alert for counter measures to be quickly enacted.
To satisfy government regulations - Almost all organizations find PAM solutions vital to keep up with growing compliance regulations from the government.
To qualify for cyber insurance - Any organization looking to qualify for a sound cyber-insurance plan requires maintaining top security controls which a PAM solution helps enforce.
To protect sensitive data - Companies need a PAM solution to handle access to critical business resources and keep their privileged data, credentials and files encrypted. Enforcing Multi-factor authentication to access privileged data makes it extremely difficult for hackers to get their hands on sensitive data.
The dynamic and fluctuating nature of cyber risks pushes organizations to keep their network secure on all fronts, and PAM helps battle the root factors that cause cyberattacks. With the threat landscape increasingly moving toward targeting privileged accounts, implementing PAM software has transitioned from an important security control to an absolute necessity.
What are the major differences between IAM, PAM, and PIM?
Identity and Access Management (IAM) - Identity and access management is a security strategy aimed at managing identities and administering control over access permissions in an IT network. IAM ensures that the right person in your organization can access the right resource for the right purpose. The pillars of IAM include (but aren’t limited to):
Identity Lifecycle Management - Creating and managing digital human and non-human identities.
Implementing Access Controls - Implementing control over which identities get access to which organizational resources.
Authorization and Authentication - Enforcing access permissions through authentication and authorization of user credentials.
Identity Governance - Supervising and tracking what identities do with their access to resources.
Privileged Access Management (PAM) - IAM vs PAM - Privileged access management falls under the umbrella of IAM. While IAM covers the canopy of identity management, PAM solution focuses on managing and governing access over business-critical resources and all privileged accounts associated with them. It encompasses tools to control elevated access and elevated permissions for identities, thus decreasing the attack surface by allowing limited privileged access with specific levels of permissions. PAM solutions primarily cover the following aspects:
Discovery of Privileged Accounts - Discovering all privileged accounts across your organization.
Vaulting of Privileged Accounts and Credentials - Securely storing and managing sensitive credentials like passwords, SSH keys, files in an encrypted vault.
Privileged Access Governance - Supervising, auditing and tracking what privileged identities do with their access to resources.
Privileged Session Management and Remote Access - Allowing users to launch remote connections to assets (RMM) and recording and monitoring all such connections (PASM).
API & Application Password Security - Securing application credentials by leveraging RESTful APIs to carry out application operations without needing physical intervention or passwords hard-coded on scripts.
Privilege Elevation & Delegation Management - Elevating applications, processes and software just when users need access to them, based on a request-release workflow.
Privileged Identity Management (PIM) - PAM vs PIM - Privileged Identity Management (PIM) is a subset of PAM solution that targets the specific need of managing and controlling highly privileged access to resources. PIM solutions are limited to discovery and vaulting of privileged accounts, enforcing password policies and monitoring privileged access. It lacks session management capabilities and just-in-time privilege elevation controls that a PAM solution encompasses. PIM solutions often have lesser integrations (SIEM, Ticketing, etc.) with industry solutions than what a PAM solution offers.
Trends in Privileged Access
Privileged Access Management has evolved over time to include various industry trends which increase the overall security posture of an enterprise.
-
Cloud PAM: Organizations nowadays choose to go for cloud solutions as they are highly scalable, agentless, and are easier to deploy. The most notable advantage of cloud-native PAM systems is the capability to quickly adapt to an organization's shifting demands without requiring major and expensive infrastructure changes.
-
Just-in-time access: This is an important feature as it reduces the attack surface by providing time-limited, temporary access to the users based on the reason provided. The access will be automatically revoked after the stipulated time.
-
Integration with Zero trust architecture: PAM integrates with zero trust architecture where the system trusts nobody by default and enforces least privilege principle to the users based on their roles.
-
AI and ML integration with PAM: Artificial intelligence and machine learning are the most trending topics in today’s digital landscape. Both AI and ML are being integrated into PAM platforms to improve the identification of anomalies, automate threat response, and provide predictive insights.
With the proliferation of cloud, cloud apps, work from home, reliance on third parties, and increased number of identities to govern. We can no longer ‘Trust but Verify’. Privileged access management aims to put verification at the front for all identities. Relevant discussions on Reddit, go over this theme.
If you’re looking to get started with PAM, like many other IT administrators – go through the Best Practices for PAM.
Securden Unified PAM can be deployed in minutes on a server on-prem or hosted on private cloud instances. Try now.



