— Modern PAM Software —
An industry-leading Privileged Access Management platform like no other.
Ditch clunky PAM software, endless implementation headaches, and sky-high costs—for good.
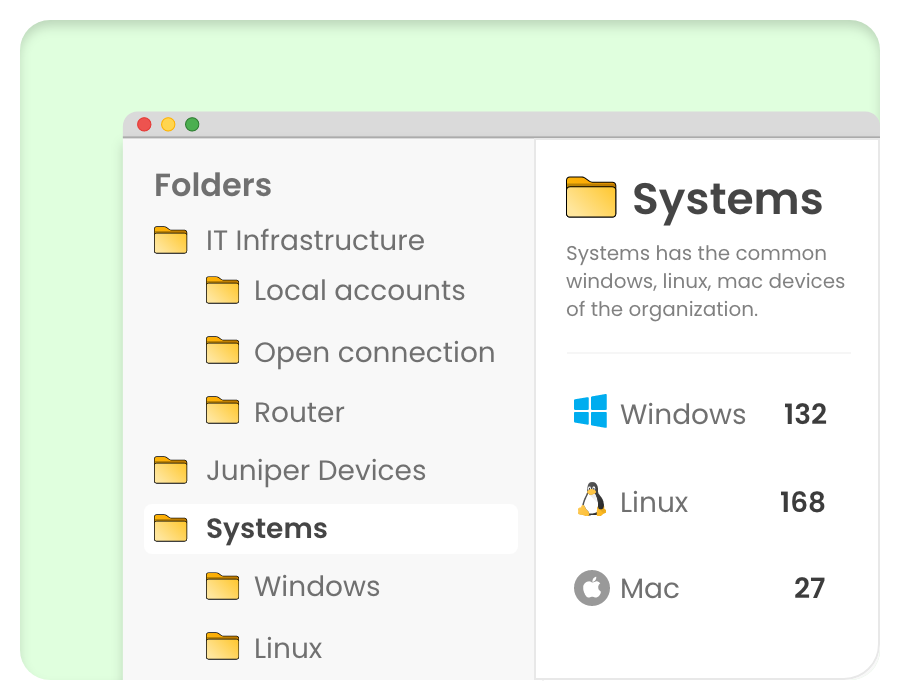
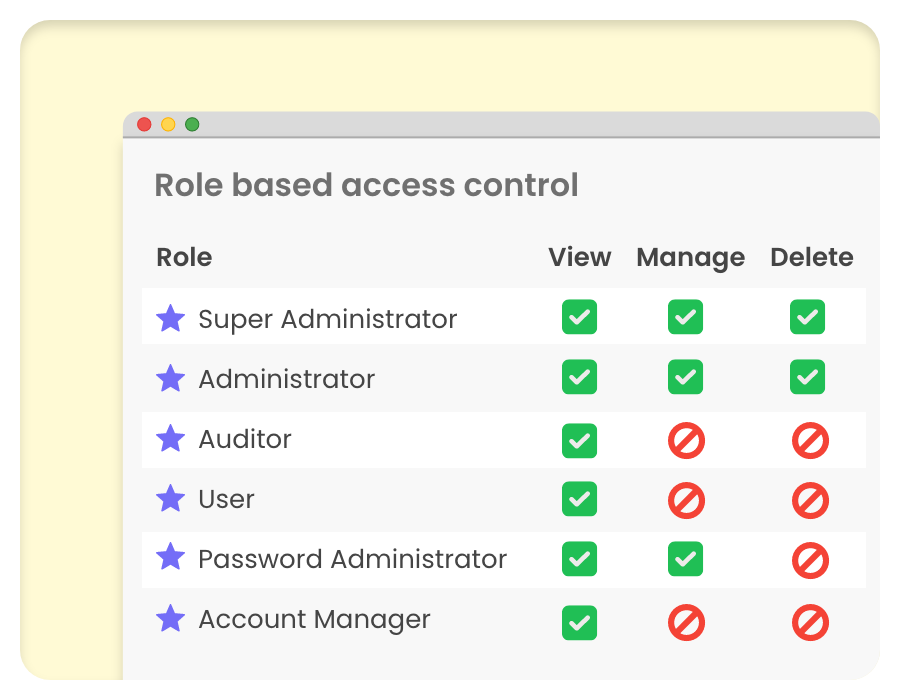
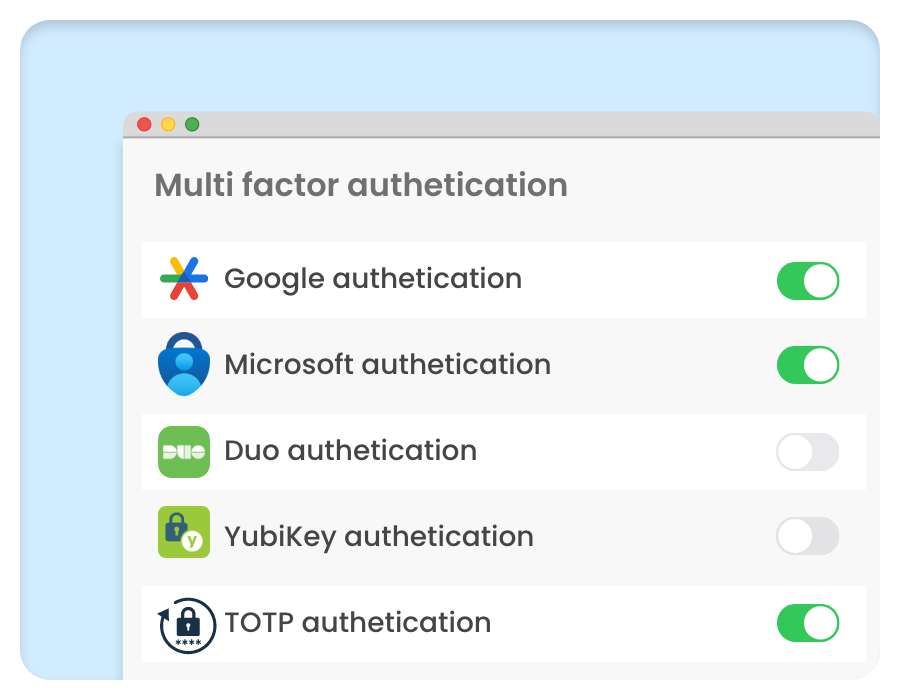
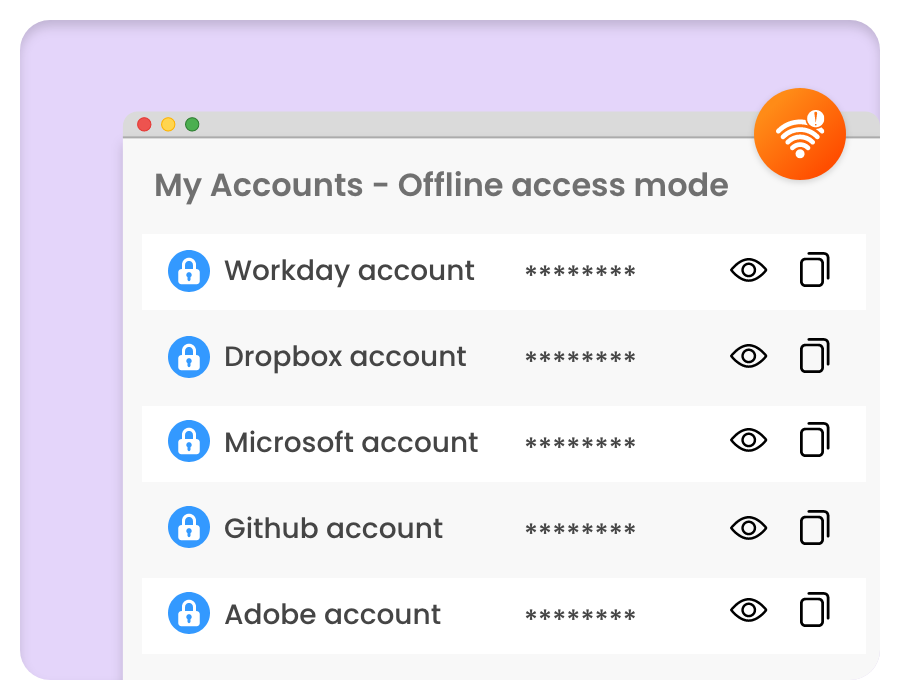
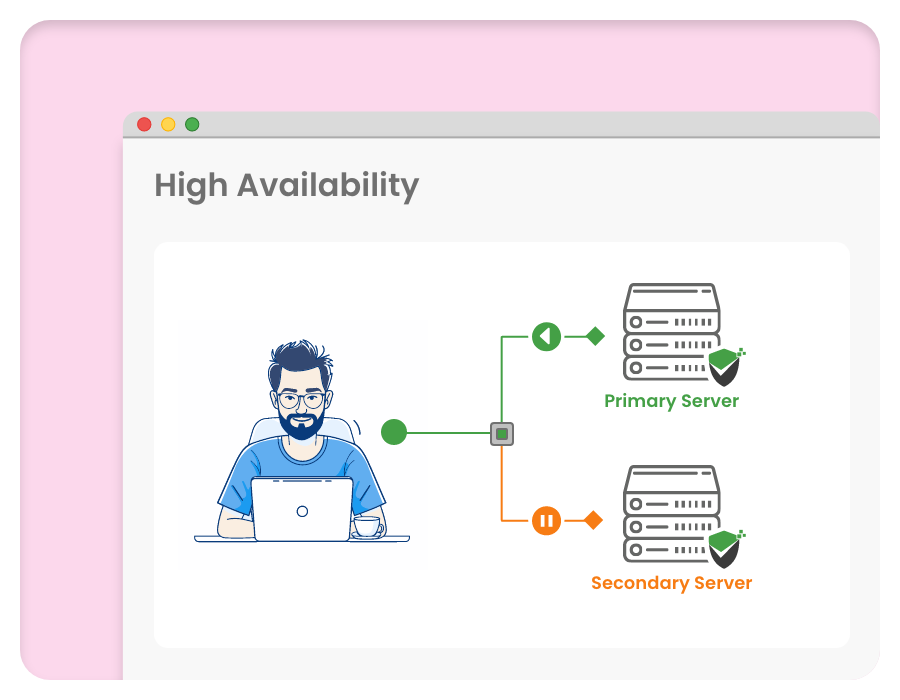
- End-to-end PAM in one unified package.
- Lightning-fast implementation, intuitively simple.
- Enterprise-grade security, unbeatable price.
- Flexible deployment—on-prem or SaaS.