It is 2:13 AM. A critical payment service is throwing an error, the incident bridge is live, and someone needs to log into a production server right now. In most banks, the urgent path looks familiar. Find the right admin account, locate the password, get a quick approval over chat, log in, fix the issue, and move on.
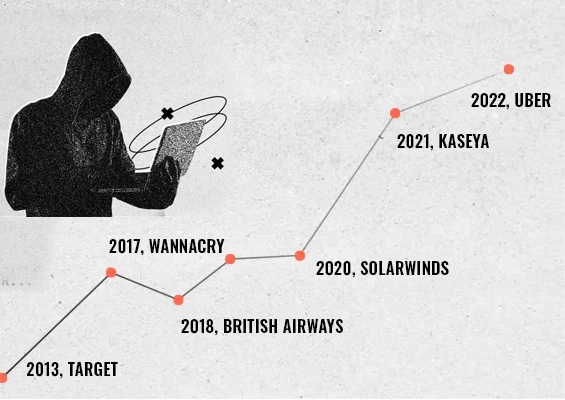
The problem is not the speed. The problem is what gets normalized in the rush. Privileged passwords get shared across people and tools, access happens outside controlled workflows, and the actions taken during the session are hard to attribute and audit later. In a regulated environment, that is not just an operational shortcut, it is a standing risk.
Privileged access is essential in banking. It powers everything from core banking maintenance to patching servers, troubleshooting outages, upgrading databases, and supporting business critical applications. The problem is not that privileged access exists. The problem starts when it becomes permanent, widely shared, poorly monitored, or impossible to audit cleanly.
In this blog, practical banking use cases where privileged access risk shows up are covered, along with the privilege controls that help financial institutions take a safer and more efficient approach without making operations painful.
Use cases where privileged access risk shows up in banks
1) Core banking, payments, and high impact platforms
Problem
Core banking systems and payment platforms need privileged access for routine maintenance, upgrades, incident response, and configuration changes.
Risk
Because these are high impact systems, a small mistake or unauthorized action can lead to outages, transaction disruption, and financial exposure.
Solution
Centralize privileged access with policies, grant time bound access instead of permanent privileges, use secure remote sessions where credentials are not exposed, and enable session monitoring and recordings for audits and investigations.
2) Removing standing admin rights on endpoints
Problem
IT teams and non-IT users who need elevated access often end up with local admin rights on endpoints to install tools, run scripts, or fix issues fast.
Risk
Keeping admin rights permanently, turns a small issue into a bigger incident. Malware spreads faster, security controls are easier to bypass, and an endpoint incident becomes an enterprise incident.
Solution
Remove local admin rights by default and allow controlled elevation only when required. Keep elevation policy driven, limit it to approved apps or tasks, and maintain visibility into who elevated what and why.
3) Infrastructure and database operations that need speed
Problem
Infrastructure and database teams need privileged access to servers, databases, and network devices for patching, upgrades, and troubleshooting.
Risk
If access is granted broadly, the risk increases. If access is restricted without a workable process, operations slow down and teams start bypassing controls.
Solution
Use role-based access policies and approvals for sensitive systems, supported by just in time privileged access that expires automatically after the task. Keep the request flow simple so it works during incidents too.
4) Third party and vendor access without long term exposure
Problem
Vendors need access for support, upgrades, and troubleshooting, especially in specialized banking platforms.
Risk
Long term vendor access, shared credentials, and accounts that do not expire increase third party risk and create audit gaps.
Solution
Provide time bound vendor access that expires automatically, use credential hidden remote sessions, apply approval workflows where needed, and record sessions to support accountability and compliance.
5) Session visibility and audit readiness
Problem
Auditors and internal security reviews ask for clear evidence of privileged activity, especially on critical systems.
Risk
When privileged access is spread across tools and manual practices, evidence is incomplete. Investigations take longer, audits become painful, and accountability becomes unclear.
Solution
Centralize logs, session records, and access trails. Ensure privileged sessions can be monitored and recorded, and generate reports that map access to users, systems, and approvals.
6) Hybrid environments across on prem and cloud workloads
Problem
Many banks operate hybrid environments, with workloads across data centers and cloud platforms.
Risk
Controls vary across environments, creating inconsistent governance. Teams end up with separate processes, separate logs, and separate blind spots.
Solution
Standardize privileged access governance across environments. Use centralized policy enforcement, consistent approvals, secure remote access, and unified audit trails so controls do not break at the boundaries.
7) SOC investigations and incident response
Problem
When incidents occur, SOC teams need quick answers. Who accessed the system. What commands were run. What changed.
Risk
Without privileged session visibility, investigations slow down. Root cause analysis becomes harder, and response timelines increase.
Solution
Enable privileged session monitoring and recordings for critical systems, paired with searchable activity logs and reports. This reduces investigation time and strengthens accountability.
8) Password resets and helpdesk load
Problem
Password resets consume helpdesk time and slow down employees, especially when access is needed urgently.
Risk
Weak identity checks during resets introduce risk. Manual resets also create inconsistent trails, which weakens audit readiness.
Solution
Use secure self-service password reset with strong identity verification, policy-based enforcement, and complete audit logging. Reduce helpdesk load without lowering security standards.
9) DevOps automation and non-human privileged access
Problem
Automation relies on service accounts, keys, tokens, and secrets to run deployments and operational scripts.
Risk
Hardcoded secrets and unmanaged service accounts are high value targets. If compromised, they provide silent access that is hard to detect.
Solution
Centralize secret storage and enforce access policies, rotation, and audit trails for secret retrieval. Ensure automation teams can work fast while keeping visibility and control.
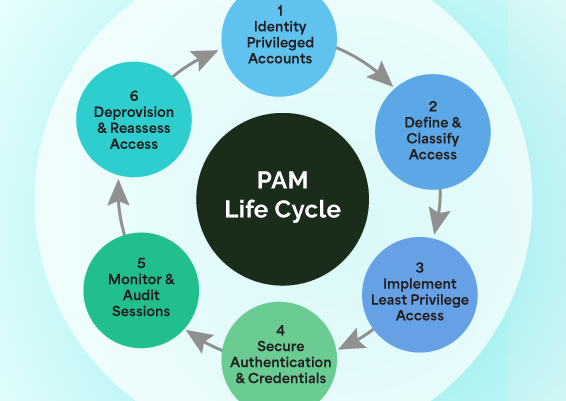
What banks should standardize as a baseline
Across these use cases, the pattern is consistent. Reduce standing privileges, make privileged access time bound, keep credentials hidden during use, apply approvals where the risk is high, monitor and record sessions, and make audit trails and reporting easy. This is not about adding friction. It is about replacing informal access with structured access that still supports real world banking urgency.
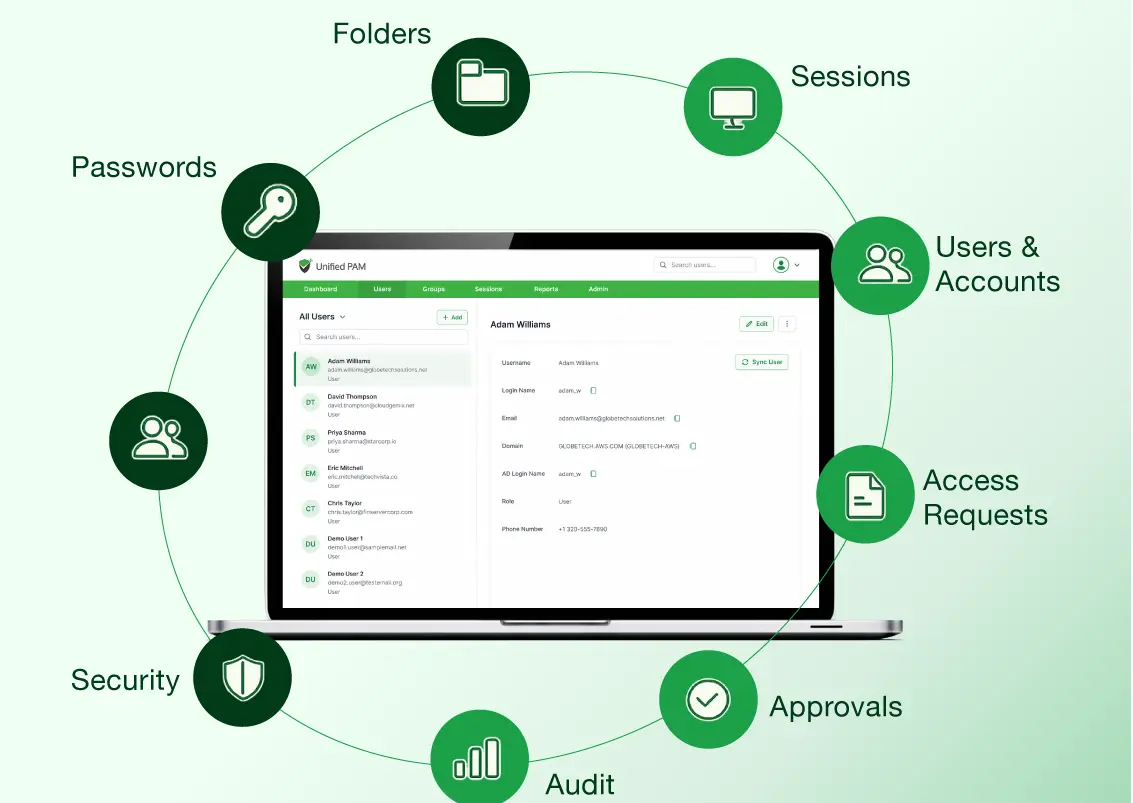
Introducing Securden Unified PAM to Secure Privileged Access in Banks
Securden Unified PAM helps banks bring privileged access under one roof with centralized control, safer access workflows, session visibility, and audit ready tracking, without slowing teams down.
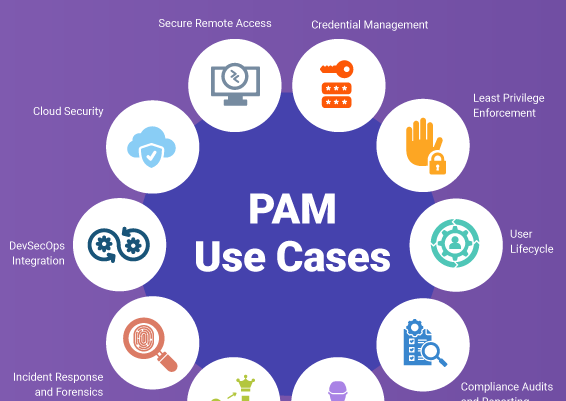
Key capabilities that map well to banking needs
-
Centralized privileged account and password management
Vault privileged accounts, enforce role-based access, and eliminate shared passwords with clear accountability. -
Automated password rotation
Rotate privileged credentials on schedule or after use to reduce exposure from stale passwords. -
Secure remote sessions with monitoring and recording
Enable controlled RDP and SSH access while keeping credentials hidden, with recordings for audits and investigations. -
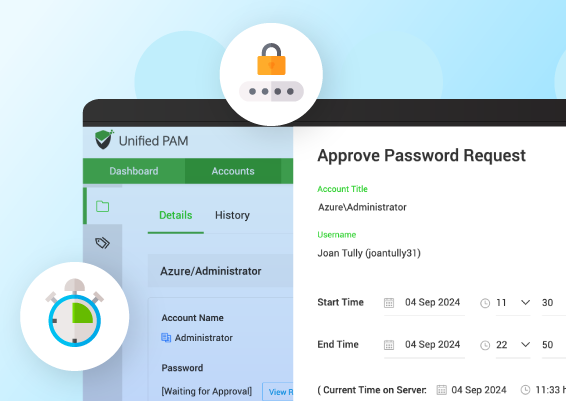
Approvals and time bound access
Add request and approval workflows for high-risk access and make privilege temporary instead of permanent. -
Endpoint Privilege Management
Remove standing local admin rights and allow controlled elevation only when needed, driven by policy. -
Reporting and audit readiness
Maintain complete audit trails and generate reports that make compliance easier. -
Self-Service Password Reset
Enable secure self-service resets with identity verification, reducing helpdesk load and improving speed. -
Service accounts and automation secrets
Control access to keys and tokens with visibility and governance, without creating silent risk. -
High availability for business continuity
Keep privileged access available during outages and incidents, so the platform does not become the bottleneck.
On the closing note…
Banks cannot remove privileged access. But they can remove privileged access risk created by permanence, invisibility, and poor governance.
When privileged access is centralized, time bound, monitored, and auditable, teams resolve incidents faster, vendors are controlled safely, audits become smoother, and the security posture improves without slowing the business. That is the outcome Securden Unified PAM is designed to support.
Click here to explore the complete set of privileged access use cases for banking and discover which PAM features help address each one.
Take the Next Step with Securden Unified PAM
You have seen the banking use cases. Now explore the PAM platform built to address them.
Discover how Securden Unified PAM helps secure access across banking environments.

































![What is Cloud PAM? [Definition, Features, Benefits, and Factors to Choose the Right One]](/images/cloud-pam/cloud-pam-blog-image.webp)