Choosing an enterprise password manager is not just a software purchase, it is a security infrastructure decision. The wrong tool leaves gaps that attackers can exploit. The right one becomes the backbone of how your organization manages credentials, controls privileged access, and meets compliance requirements.
This guide is designed to help IT teams, security leaders, and procurement stakeholders work through that decision with clarity. Whether you are running an initial evaluation, comparing shortlisted vendors, or finalizing a purchase, this resource covers everything you need: a structured checklist, a comparison framework, must-have features for 2026, the right questions to ask vendors, and warning signs to watch for before you sign a contract.
By the end, you will have a repeatable process for evaluating any enterprise password management solution against your actual environment and not just a marketing comparison chart.
What is the Criteria to Evaluate Enterprise Password Managers
A good evaluation for enterprise password manager starts with knowing exactly what you need. Use this checklist across every vendor you consider.
Security & Encryption
The foundation of any password manager is how it protects credentials at rest and in transit.
- AES-256 encryption (or equivalent): This is the industry standard for credential storage. Anything weaker is a non-starter for enterprise environments.
- Zero-knowledge architecture: The vendor should never have access to your decrypted credentials. Encryption and decryption should happen on your side only.
- Multi-factor authentication (MFA): MFA should be enforced at the platform level, not optional. Look for support for hardware tokens, authenticator apps, and SSO-based MFA.
Access Control & Governance
Storing credentials securely means nothing if access is not properly governed.
- Role-based access control (RBAC): Users should only access what their role requires. Administrators need granular control over who can view, use, share, or modify credentials.
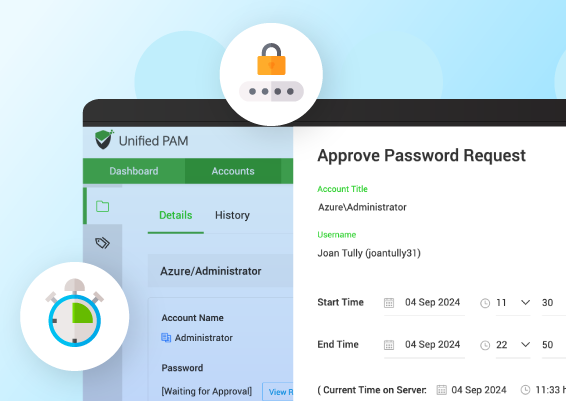
- Approval workflows: High-risk access, especially to privileged accounts, should require explicit approval before it is granted. This creates an accountability layer that audit teams and compliance frameworks require.
- Just-in-time (JIT) access: Rather than granting persistent access, JIT provisioning gives users temporary, time-limited access to sensitive credentials. This dramatically reduces the window of exposure if an account is compromised.
Password & Credential Management
The day-to-day operational capabilities matter as much as security architecture.
Secure vaulting: Credentials should be stored in an encrypted vault with strict access controls — not in spreadsheets, shared drives, or browser storage.
Automated password rotation: Passwords for privileged accounts such as service accounts, admin credentials, shared logins, and so on should rotate automatically on a schedule or after use.
Credential discovery: The solution should be able to scan your environment and identify unmanaged credentials that belong in the centralized vault.
Auditing & Compliance
In regulated industries, the ability to prove what happened is as important as preventing what should not.
Session recording: For privileged sessions, full session recording captures exactly what a user did during an access window — critical for forensics and compliance.
Audit logs: Every access, modification, approval, and exception should be logged with timestamps and user attribution.
Compliance reporting: Canned reports that help is meeting the regulatory demands of SOC 2, ISO 27001, HIPAA, or PCI-DSS save significant audit preparation time.
Enterprise Readiness
Beyond core security, a solution needs to fit into enterprise operational realities.
On-premises / Hybrid deployment: Cloud-only tools fall short for organizations that require on-premises or hybrid deployments, especially those operating in air-gapped environments, enforcing strict data residency, or needing granular control over their infrastructure.
Scalability: The solution should handle growth — more users, more credentials, more integrations — without performance degradation or architectural changes.
Integrations: Directory services, SIEM platforms, ticketing systems, and DevOps pipelines all need to connect with your password management layer.
Evaluation Checklist Table
| Capability | Must-Have | Why It Matters |
|---|---|---|
| AES-256 encryption | Yes | Protects credentials at rest from unauthorized access |
| Zero-knowledge architecture | Yes | Ensures vendor cannot access your data |
| MFA enforcement | Yes | Prevents unauthorized platform access |
| Role-based access control | Yes | Limits credential exposure by role and function |
| Approval workflows | Yes | Creates accountability for privileged access |
| Just-in-time access | Yes | Minimizes persistent access risk |
| Secure vaulting | Yes | Centralizes and protects credential storage |
| Automated password rotation | Yes | Reduces manual effort and human error risk |
| Credential discovery | Recommended | Finds unmanaged credentials across your environment |
| Session recording | Recommended | Enables forensics and compliance evidence |
| Audit logs | Yes | Supports incident response and compliance audits |
| Comprehensive reporting | Yes (regulated industries) | Reduces manual audit preparation effort |
| On-premises deployment | Depends on environment | Required for air-gapped or data-residency-constrained orgs |
| Scalability | Yes | Prevents operational bottlenecks as you grow |
| Integrations (AD, SIEM, ticketing) | Yes | Enables automation and unified visibility |
How to Compare Password Management Tools for Your IT Environment?
Features alone do not tell you which tool is right for your organization. You also need to evaluate fit — how well a solution works within your existing infrastructure, team size, and operational workflows.
Step 1: Define Your Environment
Before you open a single vendor comparison page, document your internal baseline.
- IT team size: A team of five manages things very differently than a team of fifty. Solutions designed for large enterprises can overwhelm small teams with administrative complexity. Equally, tools built for SMBs often lack the depth that large IT organizations need.
- Infrastructure type: Are you cloud-native, primarily on-premises, or operating a hybrid environment? This directly determines which deployment models are viable.
- Compliance requirements: If your organization operates under PCI-DSS, HIPAA, SOC 2, or similar frameworks, your password manager needs to actively support those requirements — not just not conflict with them.
Step 2: Compare Deployment Models
The three primary deployment models each have meaningful trade-offs.
- Cloud-hosted: Fastest to deploy, lowest infrastructure overhead, but requires trusting the vendor with your data and network access.
- On-premises: Full control, meets data residency requirements, but demands internal infrastructure and maintenance capacity.
- Hybrid: Some vendors offer a middle path — cloud management plane with on-premises credential storage — which balances control and convenience.
There is no universal right answer. The correct model depends on your compliance posture, IT capacity, and risk tolerance.
Step 3: Evaluate Operational Workflows
A password manager that disrupts how your team works will face adoption friction, no matter how secure it is.
- Access requests: How do users request access to credentials they do not currently hold? Is the process fast enough that people will not work around it?
- Shared accounts: How does the tool handle credentials shared across multiple team members and does it maintain individual accountability even when an account is shared?
- Vendor access: Third-party vendors and contractors need access to specific systems without broad credential visibility. Does the solution support temporary, scoped access for external parties?
Step 4: Compare Administrative Effort
Total cost of ownership includes the operational burden of managing the platform itself.
- Setup complexity: How long does onboarding take? Does it require professional services, or can your team handle implementation independently?
- Policy management: Creating and enforcing access policies should be intuitive. A powerful but complicated policy engine often results in misconfiguration.
- Ease of use: End users need to actually use the tool for it to work. Poor UX leads to shadow IT and workarounds.
Step 5: Evaluate Integrations
An enterprise password manager that sits in isolation from your broader security stack creates gaps.
- Active Directory / LDAP: User provisioning and deprovisioning should sync automatically with your directory service. Manual user management at scale is a security risk.
- SIEM integration: Audit logs and access events should feed into your SIEM for centralized monitoring and alerting.
- Ticketing systems: Integrations with ServiceNow, Jira, or similar platforms allow access requests and approvals to flow through existing IT workflows rather than creating parallel processes.
What are the Must-Have Features in an Enterprise Password Manager (2026)
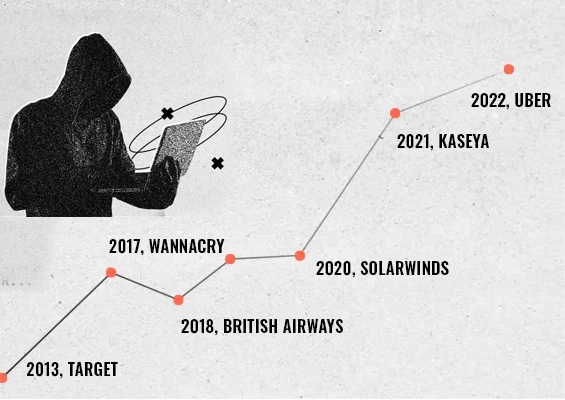
The threat landscape and enterprise IT architecture have both evolved significantly. A solution that was adequate in 2020 may have meaningful gaps today. Here is what genuinely matters in an enterprise password manager in 2026.
Core Security Features
- Encryption: AES-256 remains the standard, but implementation details matter. Look for end-to-end encryption where decryption keys never leave the client environment.
- Zero-trust access: The assumption of breach is now a baseline security principle. Your password manager should enforce least-privilege access, require verification at each access event, and never grant implicit trust based on network location.
- Credential isolation: Credentials should be segmented by team, project, or environment. A developer should not have visibility into finance credentials — even accidentally.
Operational Capabilities
- Password rotation: Automatic rotation for service account credentials, shared passwords, and so on reduces exposure windows without creating operational burden.
- Access request workflows: Structured request and approval flows mean access decisions are documented, deliberate, and auditable — not informal and forgotten.
- Secure sharing: When credentials must be shared, the mechanism should maintain encryption and access logging. Sharing via email or chat is not an acceptable alternative.
Advanced Controls
- Session monitoring: Beyond just logging who accessed what, monitoring active sessions and recording privileged activity is increasingly expected by compliance frameworks.
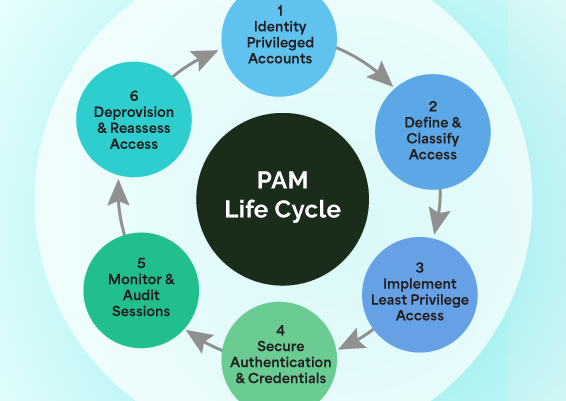
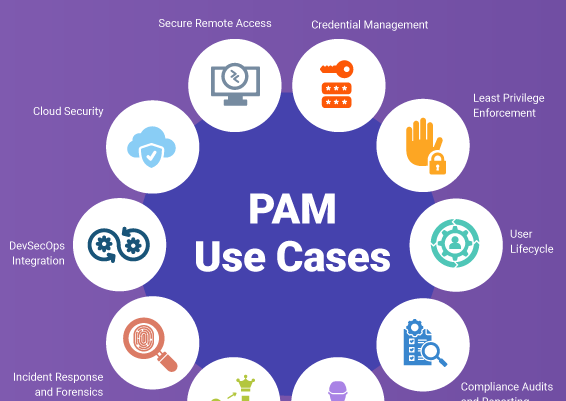
- Privileged access controls: PAM (Privileged Access Management) capabilities — managing admin accounts, service accounts, and elevated permissions, remote access to target systems are now being increasingly required in enterprise environments.
- Automation: API-driven automation for credential rotation, access provisioning, and lifecycle management integrates password management into DevOps and IT operations workflows.
Scalability & Flexibility
- Multi-team support: The platform should support multiple departments, each with independent access policies, without requiring separate instances or administrative complexity.
- Deployment flexibility: The ability to move between or combine cloud and on-premises deployment protects your investment as your infrastructure evolves.
- API access: A robust API is non-negotiable for organizations that need to integrate password management into custom workflows, CI/CD pipelines, or internal tooling.
What Questions Should You Ask Vendors When Buying an Enterprise Password Manager
Vendor demos are often designed to show you the best-case scenario. Your questions should surface the edge cases, limitations, and real-world operational details.
Security Questions
How are credentials stored and encrypted? Ask specifically whether encryption keys are ever accessible to the vendor, and how key management works in practice.
Is there a zero-knowledge model? If the vendor can technically decrypt your vault — for support, troubleshooting, or any reason — that is not a zero-knowledge architecture, regardless of what their marketing says.
Access Control Questions
Can users access systems without seeing passwords? This is sometimes called "password masking" or "blind credential injection." It means users can authenticate to systems through the platform without the underlying credential being displayed or copyable.
Are approvals enforced for privileged access? Ask for a live demo of the approval workflow. Check whether approvals can be bypassed and under what circumstances.
Deployment Questions
Do you support on-premises deployment? If so, ask for the full infrastructure requirements, including server specs, network configuration, and maintenance overhead.
What are the infrastructure requirements for your deployment model? This includes database dependencies, OS compatibility, network requirements, and storage expectations.
Operational Questions
How is password rotation handled for service accounts? Ask whether rotation is fully automated, how conflicts are handled if a dependent system does not update correctly, and whether rollback is possible.
How are shared accounts managed? Specifically, how does the system attribute individual accountability to a shared credential and what happens when a shared account password is changed?
Support & Scalability Questions
How does the solution scale to our projected user count? Ask for customer references at a similar scale, not just theoretical architecture diagrams.
What onboarding and ongoing support is provided? Understand whether implementation support is included, what SLAs look like for critical issues, and whether a dedicated support contact is available at your subscription tier.
What Red Flags Indicate a Password Manager Is Not Enterprise-Ready
Not every product that markets itself as "enterprise" is actually built for enterprise environments. These are the warning signs to watch for.
Weak Access Controls
No role-based access control: If every user has the same level of access to the vault, the tool is not built for environments where least-privilege is a requirement.
No approval workflows: Without structured approvals, access decisions are informal and unauditable. This is a compliance problem and a security problem.
Lack of Visibility
No audit logs: If you cannot produce a complete record of who accessed what and when, you cannot respond to incidents and you cannot pass audits. This is a fundamental gap.
No session recording: For privileged access, session recording is increasingly expected — both by internal security teams and by external compliance frameworks.
Limited Deployment Options
Cloud-only with no on-premises or hybrid option: This immediately disqualifies a solution for any organization with data residency requirements, air-gapped infrastructure, or strict data sovereignty policies. It is also a negotiating weakness — you have no leverage and no exit path if the vendor changes pricing or terms later.
Poor Automation
Manual password rotation only: If rotating passwords requires a human to log in and make changes manually, the process will not happen consistently. Inconsistent rotation is nearly as risky as no rotation.
No lifecycle automation: User provisioning and deprovisioning, access reviews, and credential expiry should all be automatable. Manual lifecycle management at scale leads to orphaned accounts and lingering access.
Scalability Issues
Limited integrations: A solution that does not connect to Active Directory, common SIEM platforms, or major ticketing systems will create operational silos as your environment grows.
Architecture that does not scale: Some tools are fundamentally designed for SMB environments and hit performance or architectural limits in large deployments. Ask for documented scale testing data, not just assurances.
Popular Enterprise Password Management Solutions
The enterprise password management market has matured significantly, and several vendors have established credibility across different use cases and organizational sizes.
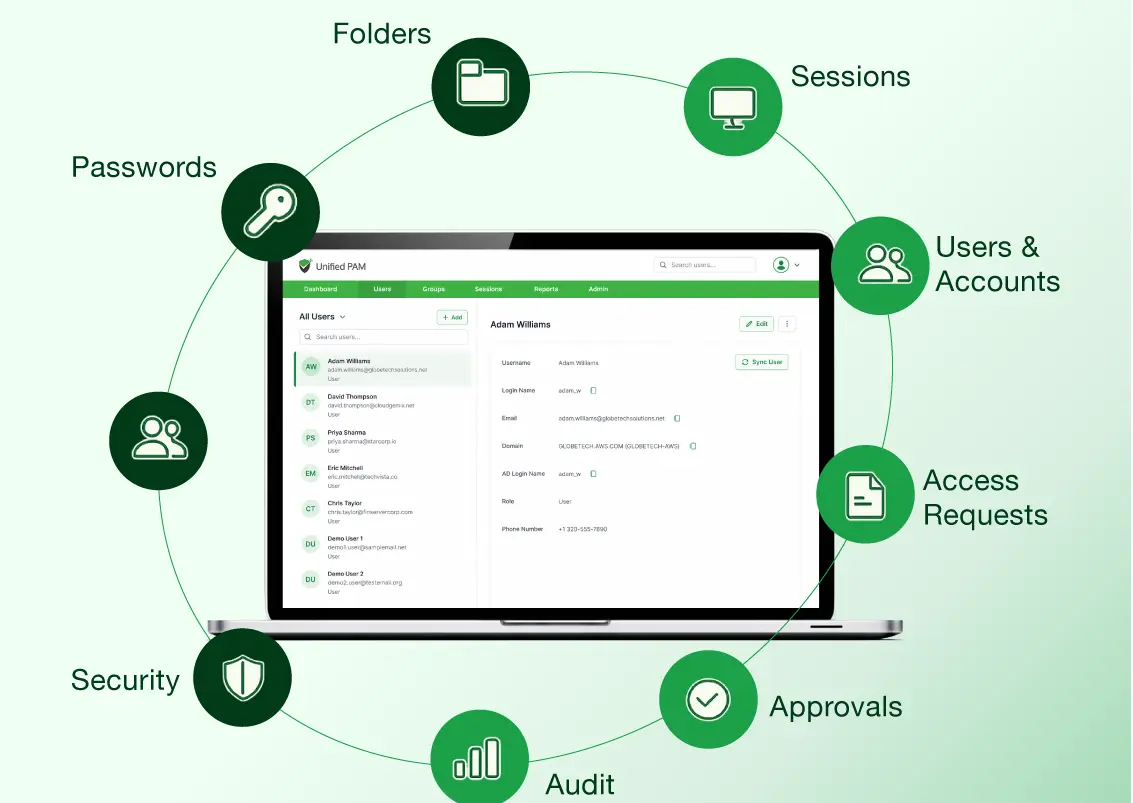
Securden offers a unified privileged access management platform that covers enterprise password management, privileged session management, and just-in-time access. It supports both cloud and on-premises deployment, which makes it relevant for organizations with strict data control requirements.
CyberArk is one of the most established names in privileged access management. It is widely deployed in large enterprise and regulated industry environments, with a comprehensive feature set that includes session recording, threat analytics, and deep compliance reporting capabilities.
Delinea (formerly Thycotic and Centrify) provides a range of PAM and password management solutions designed for enterprise scale. It offers flexible deployment options and is frequently evaluated alongside CyberArk in large enterprise procurement processes.
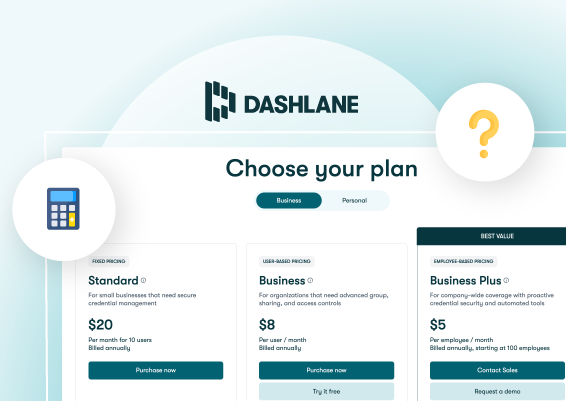
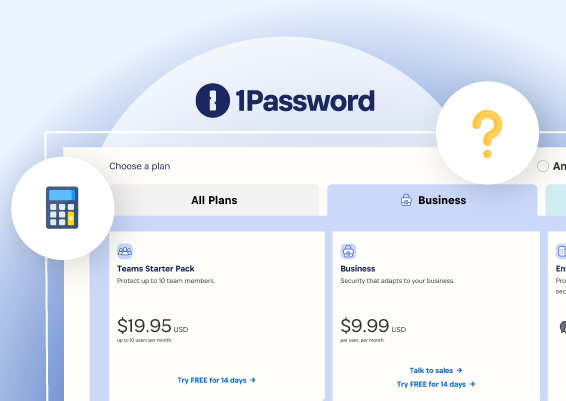
Other vendors worth evaluating depending on your environment and use case include Keeper Security (strong enterprise vault capabilities with a focus on usability), 1Password Business (popular in organizations prioritizing end-user adoption alongside security), and BeyondTrust (deep PAM capabilities with a focus on integration with existing infrastructure).
The right choice depends on your scale, compliance requirements, deployment preferences, and internal IT capacity — not on analyst rankings alone.
How to Choose the Right Password Manager for Your Organization
Different organizational contexts call for different priorities in the evaluation process.
Small IT Teams
If your IT team is lean, implementation complexity and day-to-day administrative overhead matter enormously. A feature-rich platform that requires dedicated staff to manage will either be under-utilized or become a burden.
Prioritize ease of deployment, intuitive administration, and strong vendor support. Look for solutions that can be operational quickly without extensive professional services engagement, and that do not require constant tuning to maintain basic security posture.
Large Enterprises
At enterprise scale, the priorities shift toward capability depth, compliance coverage, and integration breadth.
Focus on scalability, RBAC granularity, compliance reporting, and robust API support. Evaluate how well the solution integrates with your existing SIEM, ITSM, and directory infrastructure. Deployment flexibility matters more at this scale — the ability to support a complex hybrid environment without architectural compromise is often a deciding factor.
MSP Environments
Managed Service Providers have requirements that most single-organization tools are not designed to address.
The key requirements are multi-tenancy and client isolation. Each client environment needs to be completely separated — not just logically segmented within a shared vault, but operationally isolated so that credentials, policies, and audit logs for one client cannot be accessed in the context of another. Look for solutions with purpose-built MSP management consoles rather than workarounds built on top of single-tenant architecture.
Final Thoughts
Evaluating an enterprise password manager is not a task that benefits from rushing. The decision touches authentication infrastructure, compliance posture, operational workflows, and long-term scalability — all at once.
The framework in this guide gives you a structured path through that complexity. Start with your environment and requirements. Use the checklist to create a consistent scoring baseline across vendors. Ask specific, pointed questions rather than accepting demo-driven narratives. And take the red flags seriously — gaps in access control, auditability, or deployment flexibility do not get easier to work around after you have deployed a solution at scale.
The best enterprise password manager is not necessarily the most feature-rich one or the best-known brand. It is the one that fits your security requirements, integrates with your existing infrastructure, and can be operationally maintained by your actual team. Evaluate accordingly.
Frequently Asked Questions
What features should an enterprise password manager have?
An enterprise password manager should include AES-256 encryption, zero-knowledge architecture, role-based access control, approval workflows, just-in-time access, automated password rotation, audit logging, session recording, and support for on-premises or hybrid deployment. In 2026, zero-trust access enforcement and API-driven automation are also considered essential for mature enterprise environments.
How do I compare password management tools for my organization?
Start by defining your environment: team size, infrastructure type, and compliance requirements. Then evaluate deployment model fit (cloud vs. on-premises vs. hybrid), operational workflow alignment, administrative complexity, and integration with your existing directory services, SIEM, and ticketing platforms. Score each vendor against the same criteria for an objective comparison.
What questions should I ask vendors when buying an enterprise password manager?
Ask how credentials are stored and encrypted, whether the architecture is truly zero-knowledge, whether users can access systems without seeing passwords, how password rotation works for service accounts, whether the solution supports on-premises deployment, and how it scales to your projected user count. Request references from organizations at a similar scale and in similar compliance environments.
What are red flags in enterprise password managers?
Key red flags include the absence of role-based access control, no approval workflows for privileged access, no audit logging, cloud-only deployment with no on-premises option, manual-only password rotation, and limited integration support. These gaps indicate a solution designed for smaller or less complex environments than true enterprise needs require.

































![What is Cloud PAM? [Definition, Features, Benefits, and Factors to Choose the Right One]](/images/cloud-pam/cloud-pam-blog-image.webp)