As stories of trusted insiders causing information security breaches continue to unfold, it's time organizations woke up to internal controls basic security practices, and effective monitoring.
“May God defend me from my friends: I can defend myself from my enemies,” said French Philosopher Voltaire more than 300 years ago. This dictum proves very relevant in the current information age more than ever. Some of the worst security breaches faced by businesses are caused by trusted insiders. And it is only growing in number and intensity.
Organizations today are focusing so hard on combating external threats that they are left completely off-guard when threats come from their own people. Nevertheless, the consequences are equally devastating.
The term ‘insider’ includes not only the employees on the company rolls at the moment, but also former employees, third-party vendors, and contractors. Any of these could turn malicious anytime leading to data exposure, unauthorized access, financial loss, and reputation loss.
According to media reports, the recent high-profile ransomware attack on the software giant Accenture is suspected to have had the involvement of an insider (though it is too early to conclude anything).
Just a year ago, the FBI arrested a Russian, who reportedly offered USD 1 Million to an employee of Tesla to install malware on Tesla’s network. The Tesla employee turned down the offer and alerted his employer.
The insider threat has taken multiple dimensions and is becoming a serious concern for organizations of all types and sizes.
Before discussing how do we mitigate insider threats, let us analyze some recent trends.
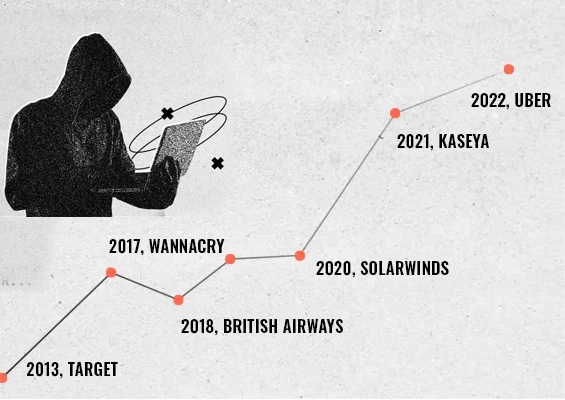
Insiders may cause one-third of all security breaches in 2021, Remote work adds fuel to fire
Security researchers and analysts have estimated that insider threats will account for one-third of all data breaches in 2021. Forrester Cybersecurity Trends states that 33% of breaches in 2021 are going to be insider threat-related, up from 25% from last year.
The total shift to remote work mode due to the pandemic seems to be adding fuel to the fire. Researchers say that uncertainties in jobs due to a ravaged economy combined with the forced remote working model is leading to increased risk due to insiders. Working in isolation outside the office environment and without the security arsenal typical of in-office work, remote workers have ample opportunities to exploit legitimate access granted to them without being quickly detected.
The 2021 Verizon Data Breaches Investigation Report reveals that
- data breaches and other security incidents caused by malicious employees working remotely take longer to detect and are more difficult to contain.
- they are causing more damage than similar incidents perpetrated by malicious insiders who are working inside office premises.
The Verizon study, considered as a gold standard, reveals that Cybersecurity incidents are very much prevalent across all the major industries with Financial and Healthcare verticals spearheading the pack in the “Misused Privileged Access” and “Lost or Stolen Assets” categories.
With most organizations contemplating a remote or hybrid working model for the foreseeable future, the above statistics assume significance for the enterprises to remain more vigilant and take proactive measures against the rising insider threats.
Insider threat is real. Let us analyze the factors that lead to insider exploitation.
Uncontrolled and unmonitored privileged access – The perfect recipe for insider exploitation
Insider exploitation mostly relates to the abuse or misuse of legitimate access. That also makes detecting insider threats very tough as these actors have legitimate access to organization systems and data. For example, data or information related to intellectual property, customers, financial data, strategic business initiatives, legal issues, etc. are sensitive and have to be accessed only by the senior executives of respective functions.
On the other hand, users with administrative access - also called IT or sysadmins, have elevated access to IT systems within the network with the unique ability to change key system configurations. While most of the privileged users use their access judiciously, there are always a few who misuse it.
According to an IBM study on insider threats,
- 40% of Insider incidents involved an employee with privileged access to company assets
- 100% of the incidents where the insider had administrative access, the elevated access played a role in the incident itself.
An incident that happened more than 8 years ago involving a former General Electric (GE) employee, Jean Patrice Delia, who had exploited valuable proprietary data and trade secrets is a classic example. Delia reportedly persuaded an IT administrator to grant him special privileges to access sensitive information. He shared the data via emails to his co-conspirator in their pursuit of starting a rival company.
Best practice approach for preventing insider threats
Malicious users with privileged access need not have to hack anything. They just need to log in. So, while spending heavily on acquiring a security arsenal to combat external threats, organizations should focus on the insider threat angle too. Combating insider threats requires concentration on certain basic security aspects.
- Access controls: There should be a clear policy on ‘who’ should get access to ‘what’ computing resources. This should be typically tied to job roles and responsibilities.
- Just-enough access: Users should get only the right level of access – not more; not less. Excessive permissions are often the starting point of attacks. The least privileged access should be the norm.
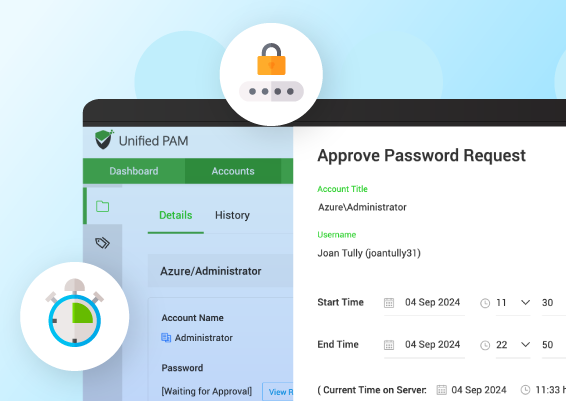
- Just-in-time access: For highly sensitive resources, the access should be just-in-time. Even trusted users will have only time-limited access.
- Continuous monitoring: All access to IT and other computing resources should be continuously monitored. Activities should be tracked. ‘Who’, ‘What’, ‘When’, and ‘Why’ of all access should be readily available. Failed logon attempts, password changes, deletion of records, unusual data transfer should all be closely monitored.
- Zero-trust access: Privileged access should follow the zero-trust model. In addition to ensuring just-in-time access, it should be context-aware too. Multi-Factor Authentication should be enforced at all levels coupled with real-time alerts and notifications on activities.
How does Securden help in combating insider threats?
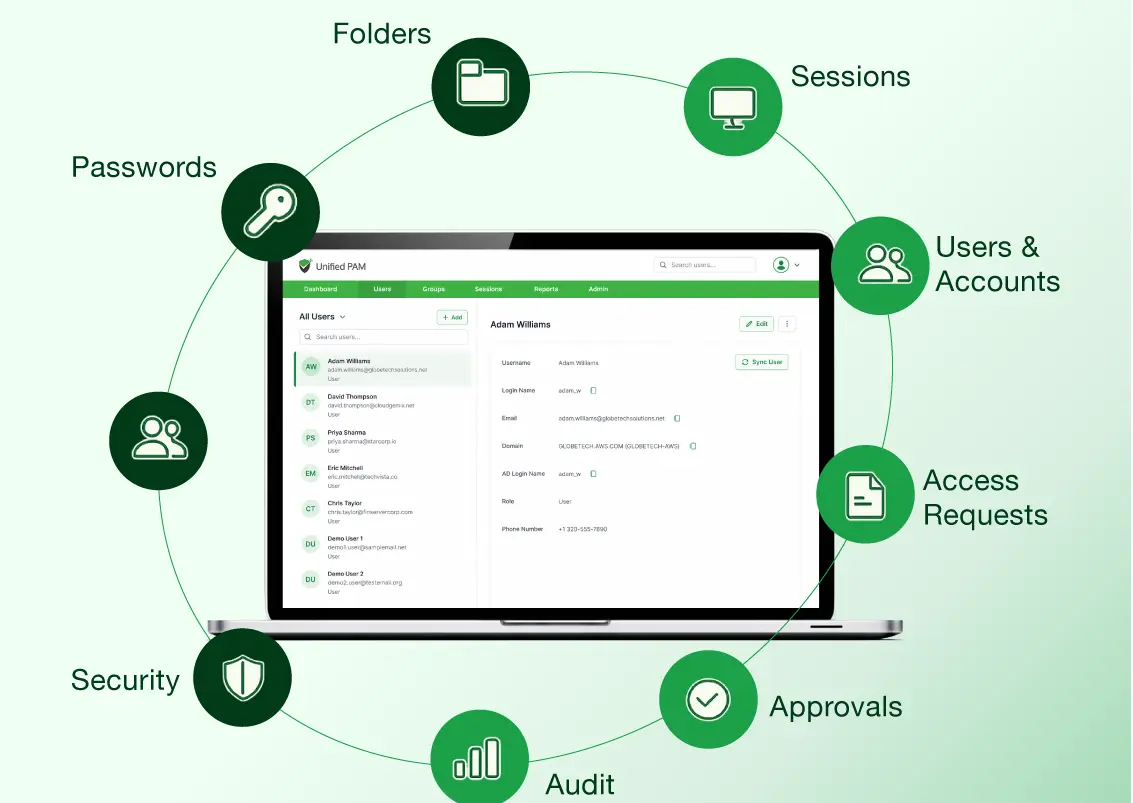
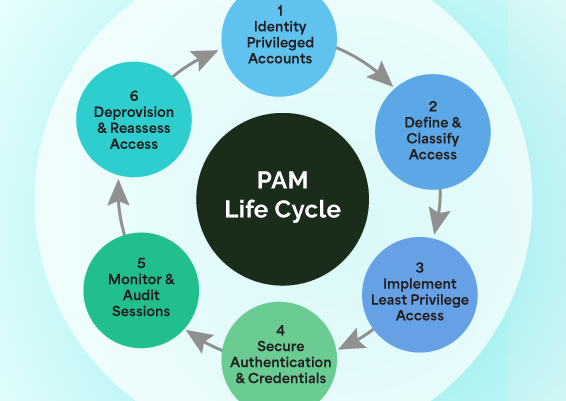
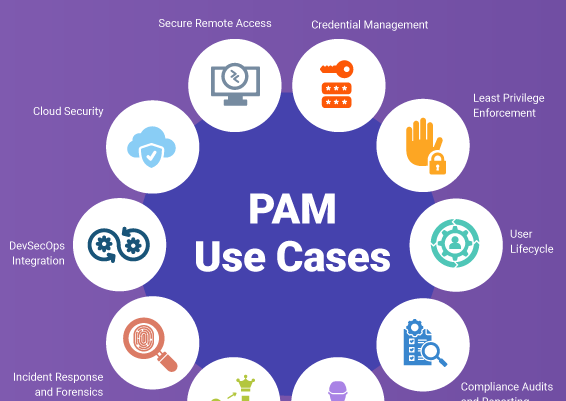
You can effectively combat insider threats by having a proper Privileged Access Management (PAM) solution in place. Securden Unified PAM serves as a full-featured privileged access security solution and helps establish a fully controlled, least privileged, zero-trust access, which is continuously monitored.
In addition, it helps in protecting passwords, enforcing password management best practices. You can ensure just-in-time and just-enough access to the IT infrastructure. Securden Unified PAM also helps in enforcing the least privilege, application, and command controls on servers and endpoints. It helps you to remove administrator privileges on computers and control application usage without impacting productivity. It seamlessly elevates applications for standard users. Through robust workflows and policy-based controls, the end-user experience remains the same even when administrator rights are removed.
Schedule a demo or start a 30-day trial now.

































![What is Cloud PAM? [Definition, Features, Benefits, and Factors to Choose the Right One]](/images/cloud-pam/cloud-pam-blog-image.webp)