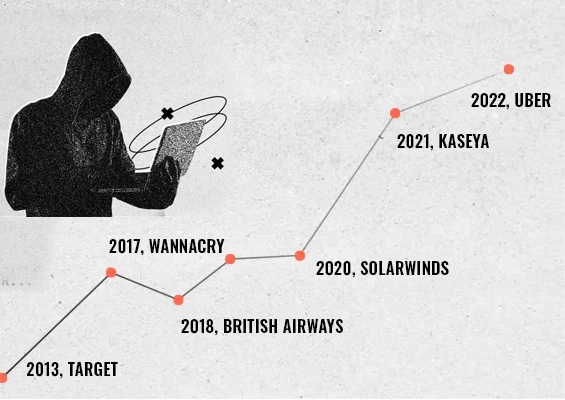
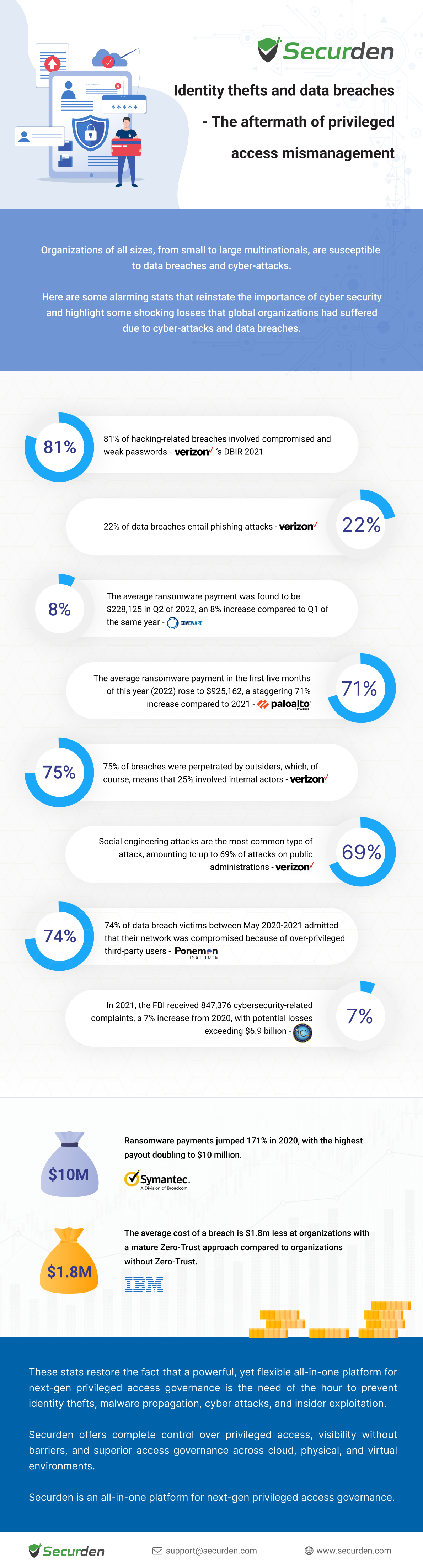
Cybersecurity is a growing concern for businesses of all sizes, as advanced hackers and cybercriminals constantly seek new ways to exploit vulnerabilities and steal sensitive information. This infographic highlights some alarming statistics about the prevalence and cost of cyber-attacks and data breaches.



























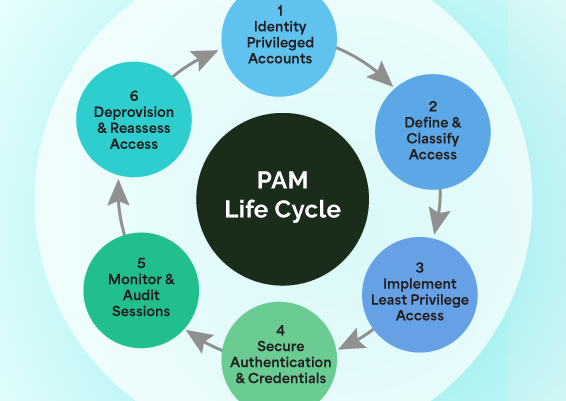
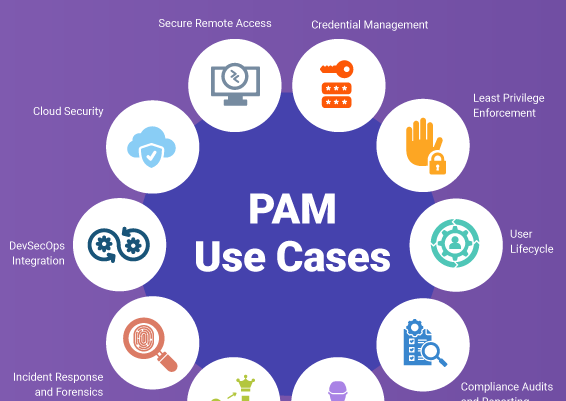






![What is Cloud PAM? [Definition, Features, Benefits, and Factors to Choose the Right One]](/images/cloud-pam/cloud-pam-blog-image.webp)