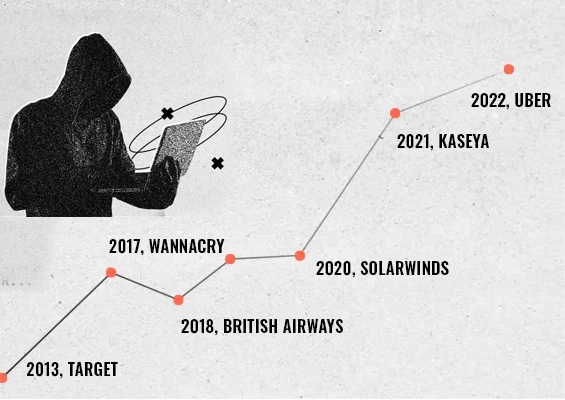
As we move close to the end of the year, the horrors of Halloween continue to haunt the land down under. Media channels are abuzz with stories of cyberattacks - probably the worst - Australia has suffered in recent times. A series of data breaches involving almost half of the continent’s population have raised serious concerns about the overall cybersecurity framework.
If it was the high profile Optus telecom towards the end of September, it was the turn of the retail giant Woolworth and, subsequently the country’s number one health insurer Medibank to hit the headlines in October. None of these attacks were sophisticated and possibly could have been averted with the right cybersecurity practices.
As easy as pie
Leaving open a public-facing API that facilitates sensitive business information - is what has apparently led to a massive attack in Australia’s history. An unprotected API was allegedly exposed to the internet, and anyone who discovered it could connect without a user ID and a password. It is hard to believe - but this is exactly what has happened in Optus, Australia’s second-largest telecom company.
The breach exposed nearly 9.8 million sensitive customer records. To get a sense of the level of sensitive data this API was granting access to: whenever an Optus customer loads their account information either via the Optus mobile app or the Optus website, an API such as the one that facilitated the data breach is used to complete the request.
All that hackers needed here was to write an automated script to complete the entire data exfiltration process. Though the basic tenets of security demand is isolating sensitive information from Open APIs, in reality, such vulnerabilities do exist. Optus has suffered a breach, but this practice is rampant everywhere. Needless to say, robust authentication mechanisms must be in place for accessing APIs. The breach is now subjected to multiple investigations.
A walk in the park
While the absolute ease with which hackers pull off massive breaches is frightening, the delay in detecting the damage is deeply worrying. Medibank, Australia’s top health insurance provider, suffered a significant breach just a few days after the Optus breach, affecting approximately 10 million customers.
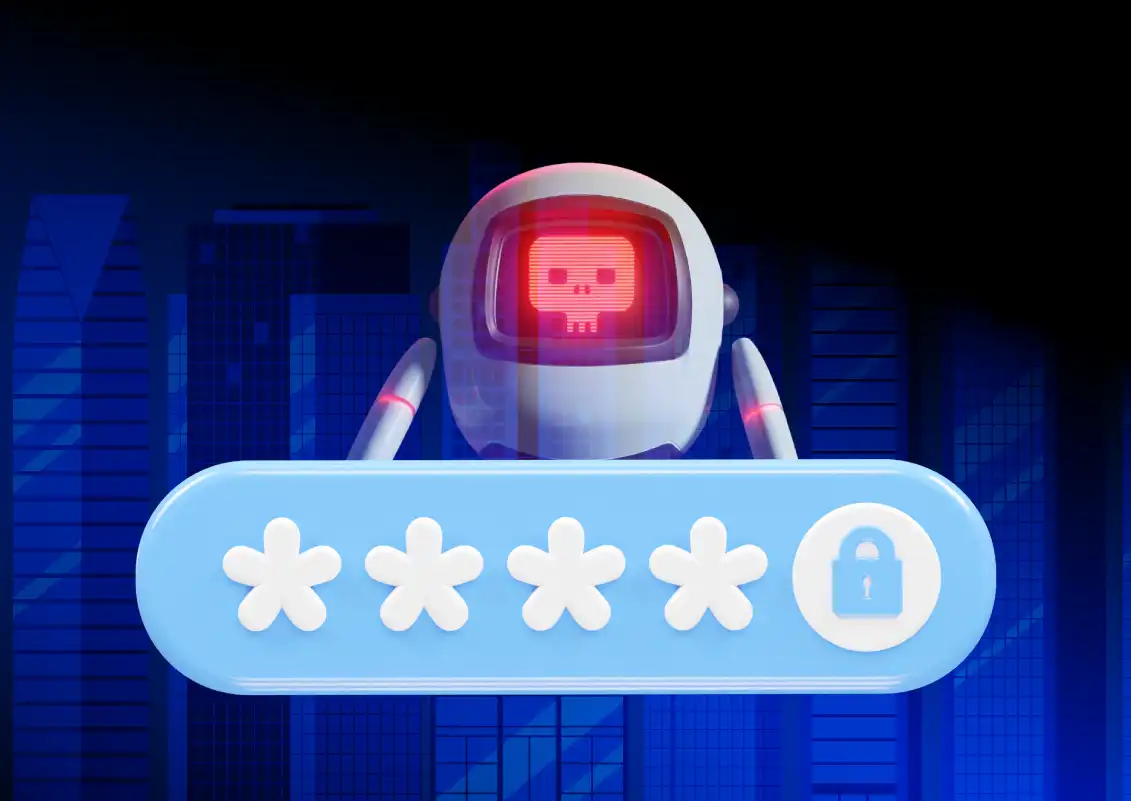
As per the initial investigations, the breach started with a hacker obtaining credentials with administrative access and offering them for sale on dark cybercrime forums. Subsequently, another group of hackers purchased the credentials and entered the Medibank network setting up not one but two backdoors.
Though the magnitude of the exact breach is not yet known, there is a widespread belief that the attacker could very well have scanned the entire network and internal systems without anyone detecting it for days. They have also apparently used a proprietary tool to extract data from the database, compress it into a zip file and later retrieve it from the network.
Stranded victims and costly damage control
The breach didn’t end there as the hackers started releasing the stolen data in tranches on the dark web demanding $10 million as ransom which the company refused to heed until now. While investigations are going on, the company’s brand reputation has been badly hit, in addition to potential legal suits and impending fines. The victims are only left to endure anxiety and fear about the potential implications of their private data online.
Privileged account credentials: Selling like hotcakes, literally!
While the Medibank breach is a major one involving compromised privileged credentials sold on the dark web, MyDeal, an online website owned by the retail giant Woolworths, suffered a similar data breach in October, affecting 2.2 million customers. As per the company statement, a compromised user credential was used to get access to customer information from the MyDeal website.
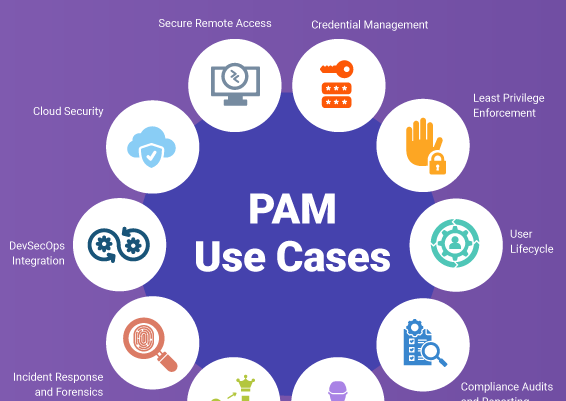
Clearly, unsecured APIs compromised privileged account credentials, and the subsequent misuse of privileged access were the primary reasons behind these incidents.
Governments can regulate; only organizations can prevent
Businesses that collect the sensitive personal information of their customers have an obligation to protect them. The spate of breaches will likely lead the Australian government to toughen cybersecurity and online privacy laws. Governments can only create regulations and impose penalties. But the protection measures are left to the organizations.
Tightening cybersecurity practices is the need of the hour. This may mean many things, including spreading cybersecurity awareness among their stakeholders. But it should start with an unfettered focus on the cybersecurity fundamentals, including protecting privileged account credentials and access. Enforcing password management best practices goes a long way in protecting the business.
Golden rules that are worth re-emphasizing again and again!
Eliminate hard-coded credentials
When applications communicate with each other, they need credentials to authenticate themselves. But a common practice for developers is hard coding those credentials inside the application, scripts, and configuration files. Hard-coded/embedded credentials in the development environment have led to massive breaches and must be avoided altogether. Instead, the credentials should be securely stored in a digital vault, and the applications should programmatically retrieve the credentials through secure APIs.
API security
APIs are undoubtedly one of the fascinating innovations of modern IT. Web, mobile, and SaaS applications are completely driven by APIs. Along with convenience comes a lot of vulnerabilities. APIs could very easily expose data if security best practices are not handled. Authorization, authentication, data filtering, proper security configuration, and checking injection vulnerabilities are all absolutely necessary.
Enforce password security best practices
Use strong, unique passwords
Every privileged account must have a strong and unique password. They also must be rotated periodically. Eliminating default and weak passwords is an absolute must.
Never Reuse Passwords
Password reuse may be convenient, but it is the number one reason for many attacks. If the same password is used for multiple accounts, you are just making things easier for the hacker.
Check against compromised credentials
Periodically review the password usage across the organization and verify if any of the passwords used by employees match the list of compromised credentials available on the dark web.
Periodically randomize sensitive passwords
Passwords of corporate accounts should be randomized at periodic intervals – ideally once in 45 days or 90 days. It is reported that it takes a few months for hackers to exploit the stolen credentials, and periodic password randomization helps avoid credential abuse.
Deploy Multi-Factor Authentication
Passwords alone may not be enough. Multi-factor authentication must be enforced at all levels.
Enforce Least Privilege
Not everyone needs admin access. Unnecessary admin privileges must be removed. Access should be granted strictly based on the user’s role and responsibilities so that they have just enough access privileges to complete their tasks. In case of genuine need, just-in-time access can be granted, subject to business approvals. Eliminating local admin rights across endpoints and elevating applications for standard users go a long way.
Monitor critical metrics
Failed login attempts and the number of password reset requests are some of the critical factors that should be continuously monitored. Abnormal patterns in these key activities might indicate an ongoing attack.
Cybersecurity training
Hackers use phishing and social engineering attacks to steal credentials. Training the users will help them identify and properly respond to such credential theft attempts, thereby protecting the business.
You need tools to achieve security basics
While the above are some of the basic security measures that organizations should focus on, the immediate question is about the implementation. Manual approaches won’t just be effective and automation is the key. Password management, privileged access management, and endpoint management solutions are designed exactly for this purpose, with automation in mind.
After all, spending on an asset that safeguards your business and gives you a better ROI than spending millions of dollars as aftermath costs of cyberattacks and rebuilding the lost reputation. Unfortunately, this is the lesson the companies that suffered the serial breach down under are learning the hard way.
How does Securden help?
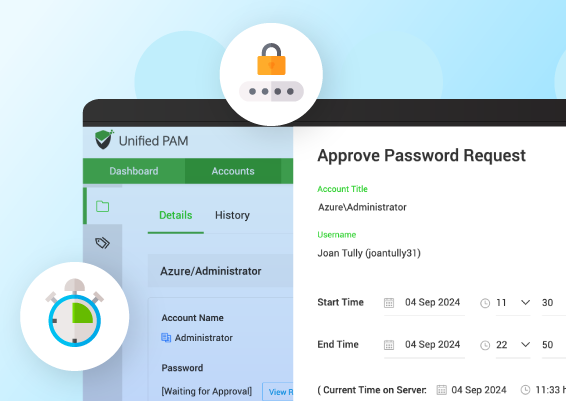
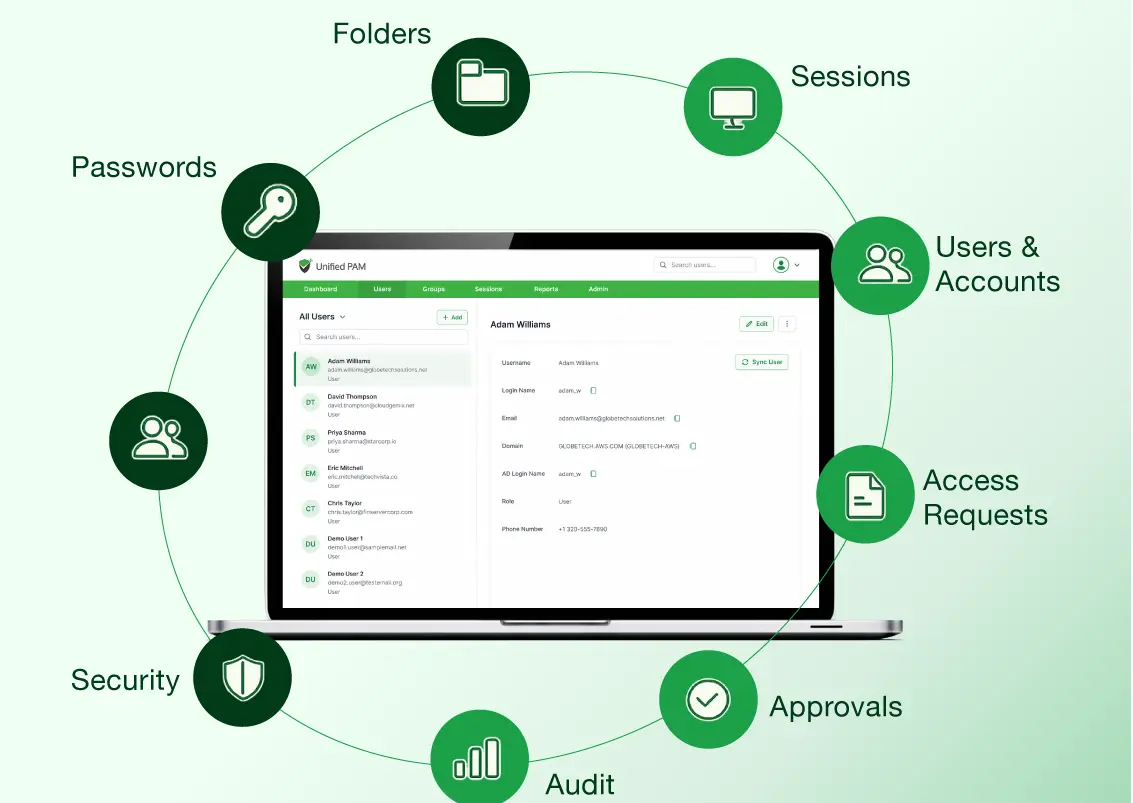
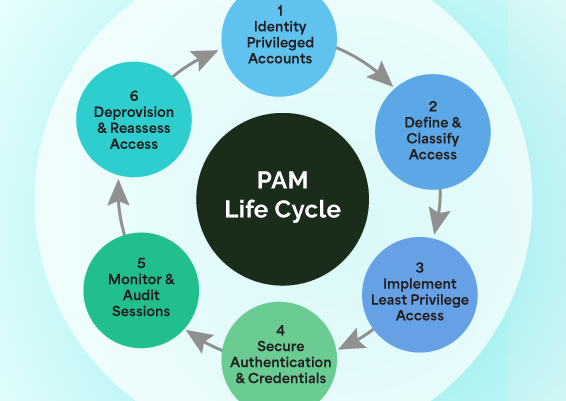
Securden offers a suite of privileged access security solutions that help organizations ensure basic security practices. Securden Unified PAM serves as a full-featured privileged access security solution and helps establish a fully controlled, least privileged, zero-trust access, which is continuously monitored.
In addition, it helps in protecting passwords and enforcing password management best practices. You can ensure just-in-time and just-enough access to the IT infrastructure. Securden Unified PAM also helps enforce the least privilege, application, and command controls on servers and endpoints. It helps you to remove administrator privileges on computers and control application usage without impacting productivity. It seamlessly elevates applications for standard users. Through robust workflows and policy-based controls, the end-user experience remains the same even when administrator rights are removed.
Schedule a demo or start a 30-day trial now.

































![What is Cloud PAM? [Definition, Features, Benefits, and Factors to Choose the Right One]](/images/cloud-pam/cloud-pam-blog-image.webp)