Let’s rewind a couple of decades for a moment. IT security, especially around credentials, was still in its early days, and password management was far from the structured discipline it is today. People chose the easiest passwords they could remember, often reusing the same one across multiple applications. In many ways, passwords were treated almost like a personal identifier, something that shouldn’t be forgotten and preferably shouldn’t be changed either.
Security teams tried to push back with policies around complexity and rotation, but enforcement was difficult. Convenience almost always won.
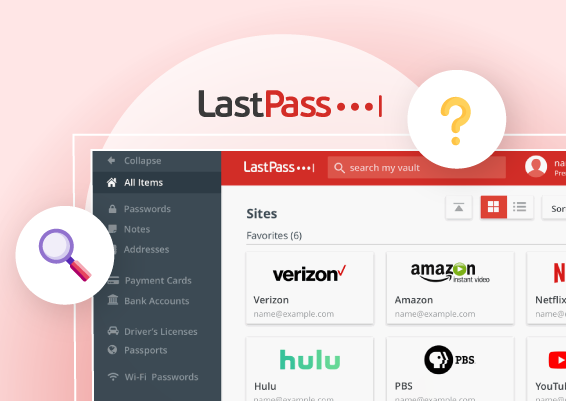
Password managers eventually emerged as the sensible fix. By storing credentials in a single encrypted vault, they removed the need for users to rely on simple, memorable passwords. Features like password generation and autofill made it much easier for organizations to enforce stronger password policies without forcing users to manually remember and type complex credentials every day.
For a while, it felt like the password problem had finally been brought under control.
Until the environment changed again.
The rapid rise of SaaS and large-scale cloud adoption introduced an explosion of applications into business and enterprise environments. The introduction of DevOps added another layer: API tokens, access keys, service accounts, and automation scripts. Credentials were no longer just passwords tied to human users. Fat-forward to today, with AI agents beginning to automate tasks and interact with systems, the number and types of credentials continue to grow.
The two things that once seemed sufficient for password management—centralized storage and strong password policies—suddenly looked incomplete.
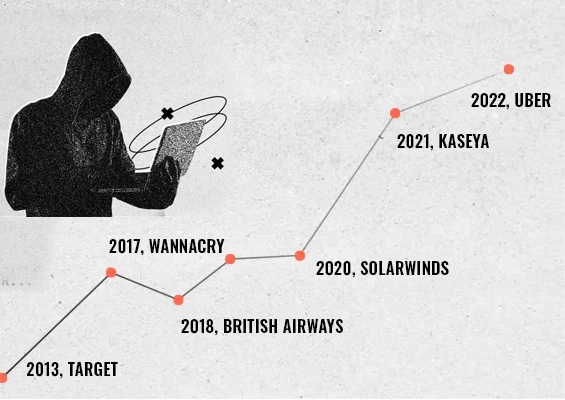
Today’s environments contain a far broader range of credentials: tokens, keys, service accounts, automation secrets, and machine identities alongside traditional passwords. This expanding credential landscape has also given attackers more entry points into systems. Unsurprisingly, compromised credentials remain one of the most common starting points for security breaches.
Which brings us to another turning point.
Password management has already evolved once, from simple credential storage to enforcing better password hygiene through policies and monitoring. Now the evolving IT environment is pushing it toward another evolution: moving towards risk-aware credential intelligence.
The Three Generations of Password Management
Before exploring how modern enterprises are adopting password management while accounting for the growing risks, it is useful to briefly understand the evolution of password management tools over time. For clarity, this evolution can be broadly categorized into three stages.
Generation1: The Vault Era – Just store it Safely
Back in the earlier times, organizational password management could be dumbed down to solving one simple, practical challenge: people are bad in remembering strong passwords, they needed a centralized place to store these strong passwords.
Password managers were built with features such as password generators and autofill, which helped address these challenges. With these capabilities, password security became more manageable—strong passwords could be created easily, and autofill simplified the process of entering them during logins.
Generation 2: The Password Hygiene Era – Strengthening Password Practices
As password-based attacks started appearing more frequently in security incidents and headlines, password manager vendors expanded their capabilities to improve password hygiene. Features such as detecting reused or weak passwords, identifying dictionary words and predictable patterns vulnerable to brute-force attacks, and enforcing organization-wide password policies became common.
These capabilities helped organizations encourage stronger password practices and reduce the likelihood of compromise due to weak or reused credentials.
However, this also revealed another challenge.
A password can be strong, unique, and never exposed in a breach—and still be involved in a security incident. This is because the real risk often lies not just in the password itself, but in how it is accessed and used. As organizations grew, challenges around controlling and monitoring password access began to emerge.
Generation 3: Risk-Aware Credential Intelligence — Understand Credential Risk in Context
Then came the cloud wave.
Organizations rapidly adopted cloud and SaaS applications, often following a cloud-first approach. The result was predictable: the number of applications—and credentials—grew dramatically. DevOps practices added another layer, introducing API keys, tokens, service accounts, and automation scripts embedded with credentials. All of these needed to be managed and secured.
And now, AI is entering the picture.
Many organizations are beginning to deploy AI agents to automate repetitive operational tasks. To perform those tasks, these agents often require access to systems—and therefore credentials. In some cases, this access can quietly expand over time as agents interact with more systems and services.
Suddenly, the credential landscape looks very different.
A password manager that simply enforces strong password policies and good hygiene is no longer enough.
What organizations increasingly need is continuous risk awareness around credentials—an understanding of where credentials exist, who is accessing them, when they are being used, and whether that access fits expected patterns.
In other words, the context behind credential access becomes just as important as the credential itself.
Consider a simple scenario. An administrator retrieves a privileged database credential during a scheduled maintenance window. That’s normal. But the same credential being accessed repeatedly at unusual hours, or from unfamiliar locations, could signal something very different. Without contextual visibility, these signals are easy to miss.
This is where a significant shift begins to take shape.
Password management starts to intersect with broader identity monitoring and privileged access security. Instead of focusing only on storing credentials or measuring password strength, the next generation of tools will increasingly help organizations identify which credentials represent real operational risk at any given moment.
In other words, password management is gradually moving from storage… to hygiene… runtime identity security
And that shift is already underway.
What Does Credential-Aware Risk Intelligence Look Like?
As password management evolves toward context-aware credential intelligence, it becomes important to understand what this means in practice for IT and security teams.
At its core, credential intelligence moves beyond simply storing passwords or checking their strength. Modern credential systems need to understand the context, behavior, and risk signals surrounding credential access.
The key question is no longer just “Is this password secure?” but rather “Does the way this credential is being accessed indicate potential risk?”
Several capabilities begin to define this next generation of credential management.
1. Contextual Credential Access
Not all credential access is equal.
A password retrieved by an administrator during a scheduled maintenance window is normal. The same credential accessed repeatedly at unusual hours or from unfamiliar systems should raise questions.
Contextual analysis focuses on the circumstances surrounding a single access event—who is retrieving the credential, when it is being accessed, where the request originates from, and whether the activity aligns with expected operational context.
In other words, contextual credential access helps answer a simple question: “Does this particular access request look legitimate given the situation?”
2. Sensitivity Awareness
Not all credentials carry the same level of risk.
A credential for a marketing SaaS tool and a credential for a production database clearly do not have the same impact if compromised. Modern systems therefore need to recognize this difference and apply stronger monitoring and controls to high-value credentials such as administrative accounts, infrastructure access, and production systems.
3. Behavioural Signals Around Credential Usage
While contextual analysis evaluates individual access events, behavioral analysis looks at patterns of credential usage over time.
Examples include:
- A user retrieving far more credentials than usual
- Sudden access to systems outside a user’s normal responsibilities
- Bulk exports or repeated vault access activity
Individually, these actions may not appear suspicious. But when viewed together, they can signal a compromised account or insider threat scenario.
Detecting such patterns is what begins to transform password managers from simple storage tools into credential intelligence platforms.
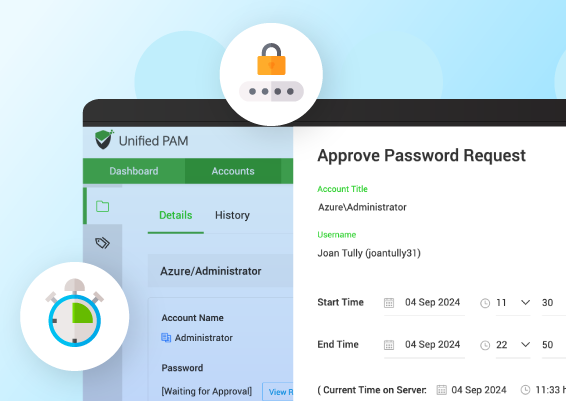
The Convergence: Where Password Management Meets Runtime Identity Security
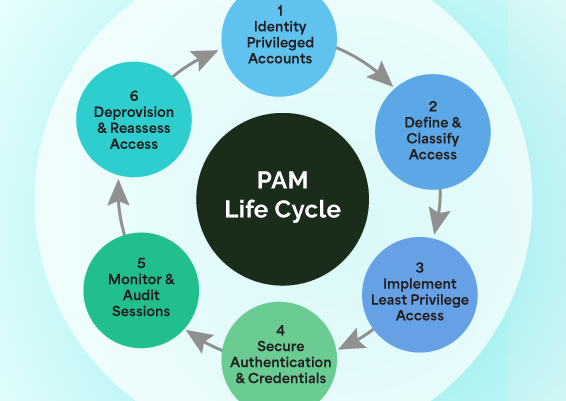
As credential risks grow, the boundaries between password management, privileged access management (PAM), and identity security are beginning to blur.
Traditionally, these systems operated separately—password managers stored credentials, identity systems handled authentication, and PAM solutions protected privileged accounts. But modern environments no longer operate in such clear silos.
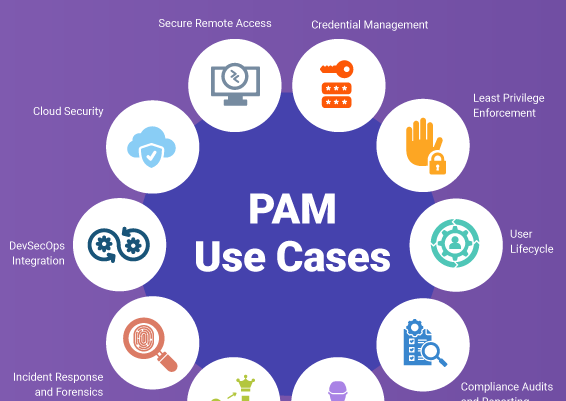
Credentials now sit at the center of human access, machine identities, APIs, automation scripts, and increasingly AI-driven systems. Securing them therefore requires not only storing them safely but also understanding how they are accessed and used.
This is where the concept of runtime identity security begins to emerge. Instead of focusing only on authentication or static access permissions, runtime identity security looks at how identities and credentials behave while systems are actively running—monitoring who is accessing credentials, how they are being used, and whether that activity aligns with expected patterns.
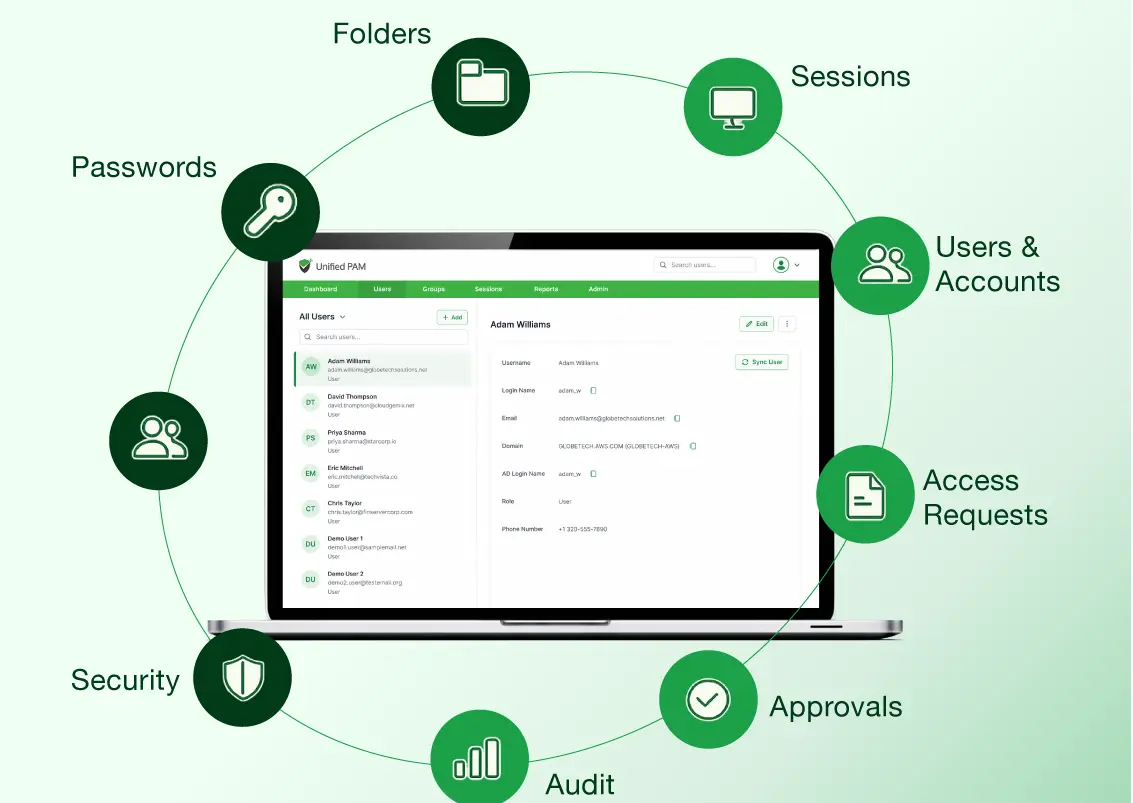
As a result, password management platforms are expanding with capabilities such as access controls, monitoring, audit visibility, and credential usage insights, while identity and PAM systems increasingly incorporate credential management.
This shift reflects the growing convergence of password management, privileged access management (PAM), and identity security into a more unified approach to securing credentials and identities.
The Road Ahead
The journey of password management reflects how the security landscape itself has evolved—from simply storing credentials safely, to enforcing stronger password practices, and now toward gaining complete visibility and control over how identities and credentials operate across increasingly complex environments.
As organizations scale, the challenge is no longer just managing passwords—it’s securing a growing mix of human users, machine identities, and even AI-driven agents, all interacting across distributed systems. This demands a more unified, context-aware approach to identity security.
Platforms like Securden are leading this transition by bringing together password management, privileged access controls, and broader identity security capabilities into a single, cohesive control plane. By eliminating fragmented tools and centralizing visibility and policy enforcement, organizations can reduce complexity, close security gaps, and build a more resilient foundation for modern identity security.
To learn more about Securden’s unified identity security platform visit https://www.securden.com/ or reach out to us at support(at)securden(dot)com.
FAQs
1. What should organizations look for in a modern password manager?
Beyond just storing passwords, modern password managers are increasingly focused on giving visibility into how credentials are actually used, who accessed them, when, from where, and for what purpose. This kind of context helps teams better assess risk and spot anything unusual.
At the same time, it’s no longer just about human users. Modern environments also involve non-human identities like DevOps secrets, tokens, service accounts, and even AI agents—all of which need the same level of visibility and control.
2. How do modern password managers handle machine identities and non-human credentials?
Modern password managers have evolved to handle more than just human user credentials. Today, they also manage non-human identities such as service accounts, API keys, tokens, SSH keys, and secrets used in DevOps and automation workflows.
Instead of leaving these credentials scattered across scripts, configuration files, or pipelines, modern solutions bring them into a centralized vault, where access can be controlled, rotated, and audited. This reduces the risk of hardcoded secrets and unauthorized access.
More importantly, they provide visibility into how these credentials are used—tracking when they are accessed, by which system or process, and whether the usage aligns with expected behavior. This helps organizations maintain control over machine-driven access, which is often harder to monitor than human activity.
3. What is the best password manager for enterprises with complex environments?
The best password manager for enterprises with complex environments is one that goes beyond basic vaulting to offer strong access controls, audit visibility, and support for a wide range of credentials—including service accounts and API keys.
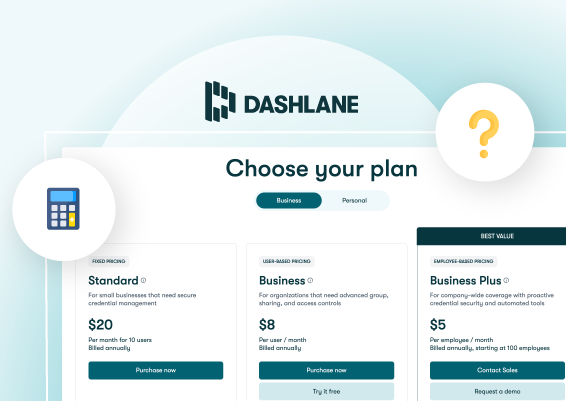
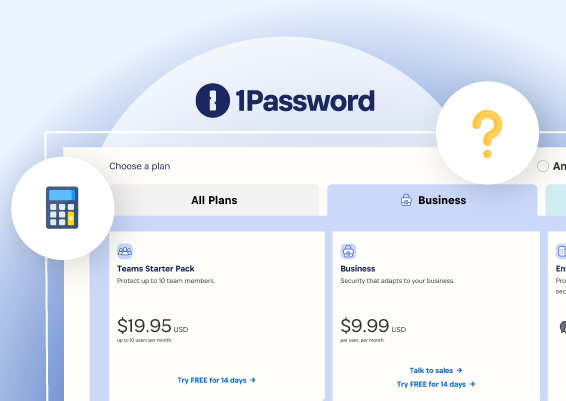
Solutions like 1Password Business, LastPass Business, Dashlane Business, and Bitwarden Enterprise are commonly used, with strengths in usability, scalability, and ease of deployment.
However, as environments grow more complex, many organizations are looking for more unified approaches that bring together password management with deeper access control and visibility. Platforms like Securden, for example, extend beyond traditional password management by combining credential management with access governance and monitoring—helping reduce complexity while improving control.
Ultimately, the right choice depends on how well the solution fits your environment and provides both visibility and control over credential usage.
4. How can a password manager help with compliance and audit requirements?
A password manager helps with compliance and audits by centralizing how credentials are stored, accessed, and managed. It enforces policies like strong passwords, controlled access, and regular rotation, while maintaining detailed audit logs of who accessed what and when.
This makes it easier for organizations to demonstrate accountability, meet regulatory requirements, and quickly provide audit evidence without manual tracking.
5. Which password manager supports DevOps secrets, API keys, and service accounts?
Password managers that support modern enterprise use cases typically go beyond user credentials to handle DevOps secrets, API keys, and service accounts. Solutions like Bitwarden Enterprise, 1Password Business, and Dashlane Business offer varying levels of support for these use cases.
However, as environments become more complex, some platforms—like Securden—are designed to manage both human and non-human credentials in a more unified way, with better access control and visibility over how these secrets are used.

































![What is Cloud PAM? [Definition, Features, Benefits, and Factors to Choose the Right One]](/images/cloud-pam/cloud-pam-blog-image.webp)