Trusted by businesses of all types and sizes across the globe




















































Discover and manage administrator, service, and web app passwords, keys, and identities. Automate management with approval workflows. Centrally control, audit, monitor, and record all access to critical IT assets.
Integrate with SIEM, ticketing system, MFA, SSO, and directories. Manage large, complex, distributed environments.




















































Gain holistic visibility and control over client privileged access from a single, unified platform.

Laurent C,
Director Technology,
Elit Technologies
One of the many things we love about Securden Password Vault [for Enterprises] is its amazing access control features (for example, we can hide folders for some users while giving permissions to others). Plus, the ability to launch web RDP and web SSH sessions has been really helpful for us. Their customer support is extraordinary—we’ve always received immediate solutions to any problems we’ve faced.

Tim N,
Infrastructure Engineer,
UFS TECH
This is a great password vault for on-prem use. With easy imports, granular permissions, failover configuration, and excellent support, it's a no-brainer. We had it up and running within hours, integrating seamlessly with Active Directory and Duo.
As an MSP with multiple teams using various vaults daily, the granular permissions help us control access and keep things simple. Unlike other solutions that bundle privileged access management and other features at a high cost, Securden offers a well-built, straightforward on-prem password vault with great support at a great price. We've highly benefited from consolidating and controlling both internal and customer passwords for our MSP.

Olivia Grimstead,
Process Manager,
NRTC Managed Services
I can never rave enough about Securden. We came to them with a large obstacle that other password managers could not achieve, and they built it out within a month. Anytime we have an issue, they are immediately on it. They are very communicative, and responsive.

Bill D,
IT Director
Excellent tool for securely storing passwords, SSH keys, and other credentials. It provides an easy-to-use interface to managing password access permissions (sharing), and a quick way to view who has access to specific passwords.
I also find their support team to be excellent. They are quick to answer questions, and they have also released updates to the product to specifically address a feature that we needed. They are great to work with.
Cameron Fisher,
Identity & Access Management Analyst,
ITS University of the Fraser Valley
It's a great password manager that's both user-friendly and easy to set up. The cost is affordable and offers excellent value for any team. Setting it up is quick and straightforward, with support for a wide range of integrations. Customer support is top-notch—always prompt and willing to assist. The SSH and RDP integrations were unexpectedly useful and really helped our team members transition smoothly. We needed an affordable password vault that could handle various account types across multiple IT teams, and Securden fits the bill perfectly.

Kieran Billing ,
IT Manager,
Littlefish
Securden has proven absolutely invaluable in securing and maintaining all our accounts and passwords, especially the break glass accounts as we had to deal with a lot of them. The ability to write back passwords and reset password remotely is great. Also, customer support is amazingly helpful, they fix the issues immediately for us, and if we have a new request, they make it available in the next release within a couple of weeks. Overall, the product works brilliantly with little to no issues.

Executive Sponsor,
Information Technology and Services
As a managed service provider, I needed a way to centrally and securely store the credentials we use to manage our customers environments. Securden Password Vault enables me to do this with all of the granular access control, multi-factor authentication and access reporting that I need. I am very pleased with the product and would recommend it to any managed service provider looking to maintain a central credential store. The password policy, which includes both strength and duration of passwords, with the ability to generate a password that meets the policy is also very powerful. This central store, accessed from anywhere with an internet connection and also from a mobile app has enabled us to realise our goal of not communicating passwords over email or storing passwords in insecure locations.

Mike Kanakos,
System Administrator, Active Directory Expert,
Align Technology
The software has a super-clean interface, pretty slick, and is easy to understand. The product is pretty deep in functionality and I really just scratched the surface on what it can do and how well it works.
Massimo G,
IT Manager,
EVIN SRL
After trying countless password managers, Securden's on-premise solution stood out as the clear winner. Being able to share passwords securely with my colleagues has been a huge time-saver. It's incredibly user-friendly and integrates seamlessly with our browsers. And let's not forget about the added security of 2FA – it's a must-have these days.
Mark Jasek,
Network and System Administrator,
Holstein Canada
We've found Securden to be really easy to set up and incredibly reliable as an on-prem solution. It offers high availability and excellent support—I usually get a response back within an hour. Our end users have no trouble using the Chrome extension, and the autofill works perfectly. Over the years, it's been very dependable for us and regularly gets updates with new features. With minimal training, rolling out Securden was straightforward, and our users now use it daily.

Jacob V,
Systems Engineer
We have been utilizing and implementing Securden over the past year and this product has provided us with a way to allow our end users to run programs and features with administrative credentials without being a full blown administrator on the machine. This has been a great way to minimize the security risk in our environment.

Ricardo P,
Senior Network Security Engineer
I got answers for every question, during trial and afterwards. Support was fast and efficient. PAM got our own passwords safe and gave us a single, centralized way to manage customers' passwords and remote access through a single interface. Price tag is very good as well.

Jeff K,
Senior IT Administrator
I like that the database is encrypted and in-house. We really didn't want to store anything in the cloud, much less any of the major brands that seem to be hacked more which we didn't want any part of.
Rick Brooks,
One of the Largest Telecommunication Companies
Since adopting Securden in 2021, it's proven to be an invaluable asset to our IT team, exceedingly even our stringent security standards. This powerful tool automates password management, saving us hundreds of hours annually. Its centralized portal functions as a secure launchpad for our users to access critical systems via a controlled environment, eliminating the risks associated with password sharing. Securden has significantly enhanced our overall security posture.

Luis Millares,
TechRepublic
Securden is best for organizations looking for a password management tool primarily for auditing and reporting purposes, given its extensive audit trail and reporting capabilities. Its folder tree navigation system also makes it a great choice for companies that want an efficient way to organize their passwords.
Joseph White,
System Administrator,
Financial Services
Securden is a standout on-prem password manager. It has everything we need and more. Their support is top-notch. We encountered a small bug, but their team was incredibly helpful. They worked quickly to resolve the issue, and within a day, they released a new version with the fix. It's rare to find such a responsive and dedicated support team.
Luca S,
Administrator, IT Software
We've been using Securden since late 2021 and have been consistently impressed by their ongoing improvements. Getting started was a breeze, and our team quickly adopted the password vault as an essential tool. We’ve had minimal issues since integrating Securden, but when we did, customer support was incredibly responsive. The range of features is fantastic. There was only one feature we missed, but Securden assured us it's in their development plan.
Over 80% of security breaches involve stolen credentials and exploitation of privileged access. Securden PAM strengthens privileged access security and secures your infrastructure from internal and external threats.
Store, manage and control access to all privileged accounts, including passwords, keys, certificates, and documents from a central database. Prevent identity thefts and unauthorized access to credentials.
In the absence of centralized management, privileged accounts are left uncontrolled and unmonitored resulting in chaos. Consolidate accounts, establish access controls, enforce policies, eliminate system lockouts, and improve the efficiency of IT teams.
Industry and government regulations mandate controlling and continuously monitoring privileged access. Ensure and demonstrate compliance to various regulations by enforcing policy-based controls, audit trails and reports.



Securden helps you gain centralized control over admin passwords and complete visibility over privileged access with an easy-to-use, simple to deploy and a highly affordable solution.
Discover, consolidate and securely store all your privileged accounts in a centralized vault. Organize accounts into folders reflecting your company's hierarchy.
Securden's discovery engine scans your network and discovers systems (Windows, Linux and Mac), databases (MySQL, PostgreSQL, Oracle and MSSQL) and network devices. It also imports the privileged accounts from the systems and devices. In the case of Windows, Securden fetches local admin accounts, domain accounts and service accounts on member servers. It also traces the dependencies of service accounts.
You can organize accounts in nested folders reflecting the organizational hierarchy with the flexibility of assigning permissions at any level. Sensitive data are encrypted using AES-256, the strongest known, military-grade algorithm.
Securden PAM stores sensitive data and you can control access to records and privileges to perform various functions within the application based on user roles.
Securden provides five pre-defined user roles with well-defined access scope and privileges. At the application level, the ability to add accounts, change passwords, create and manage users, enforce password policy, export data, view audit trails, generate reports, and change settings can all be controlled through roles.
By enforcing users to authenticate through two successive stages to access their Securden account, you can successfully prevent any possible accidental or intentional unauthorized access to Securden.
Securden's native authentication or Active Directory authentication serves as the primary authentication mechanism. Additionally, users can be forced to authenticate through Google Authenticator or verification code sent to their email address as the second authentication factor. You can selectively enforce any option as the second authentication factor for different users as required.
IT staff on remote locations or client site without access to Securden, can use the secure offline access mechanism.
Securden allows you to export your passwords in the form of an encrypted HTML file for secure offline access. The file could be periodically sent to your email address too. The offline interface is the same as the online interface.
You can open the offline copy using any standard web browser from any device, including mobile devices. As the offline copy is encrypted and the encryption key is known only to you, no one else can access the data.
Unexpected downtime or system crash could take a heavy toll on the business continuity and data security of any organization.
Securden comes with a robust redundancy architecture allowing you to have primary and secondary application servers. If the primary server goes down, users can seamlessly connect to the secondary server and get uninterrupted access to credentials.
It also comes with provision for periodic backup of the database and a smart recovery manager that takes care of a quick recovery in the unlikely event of a database crash.
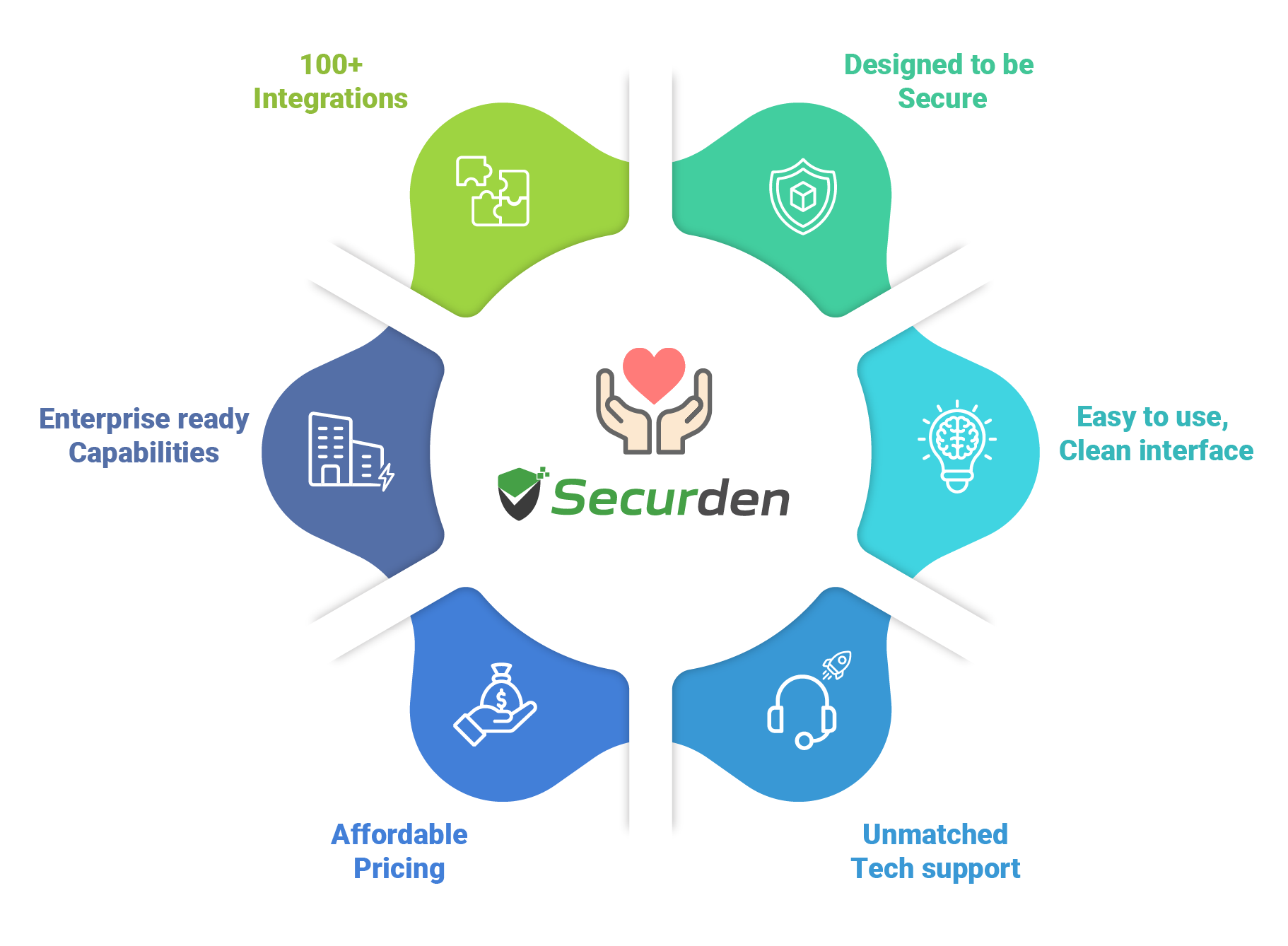
At Securden, we're fanatical about one thing:
Creating amazing products that combine security, simplicity, and affordability.
Organizations of all types and sizes - from small businesses to very large enterprises - are relying on Securden for information security.
Here's what sets us apart from the rest.
IT security specialists from a UK-based firm performed various penetration tests and concluded that Securden is well-built with a top-notch security model. Learn More.

-- Experts from Agile Infosec, London.

Securden technical consultant will walk you through the important features demonstrating how you can safeguard the keys to your kingdom.
